VPN vs Browser Proxy Extension: Key Differences
Why a browser proxy extension is not the same as a full VPN — what each protects, where each falls short, and which is right for Hong Kong users in different situations.
Why a browser proxy extension is not the same as a full VPN — what each protects, where each falls short, and which is right for Hong Kong users in different situations.
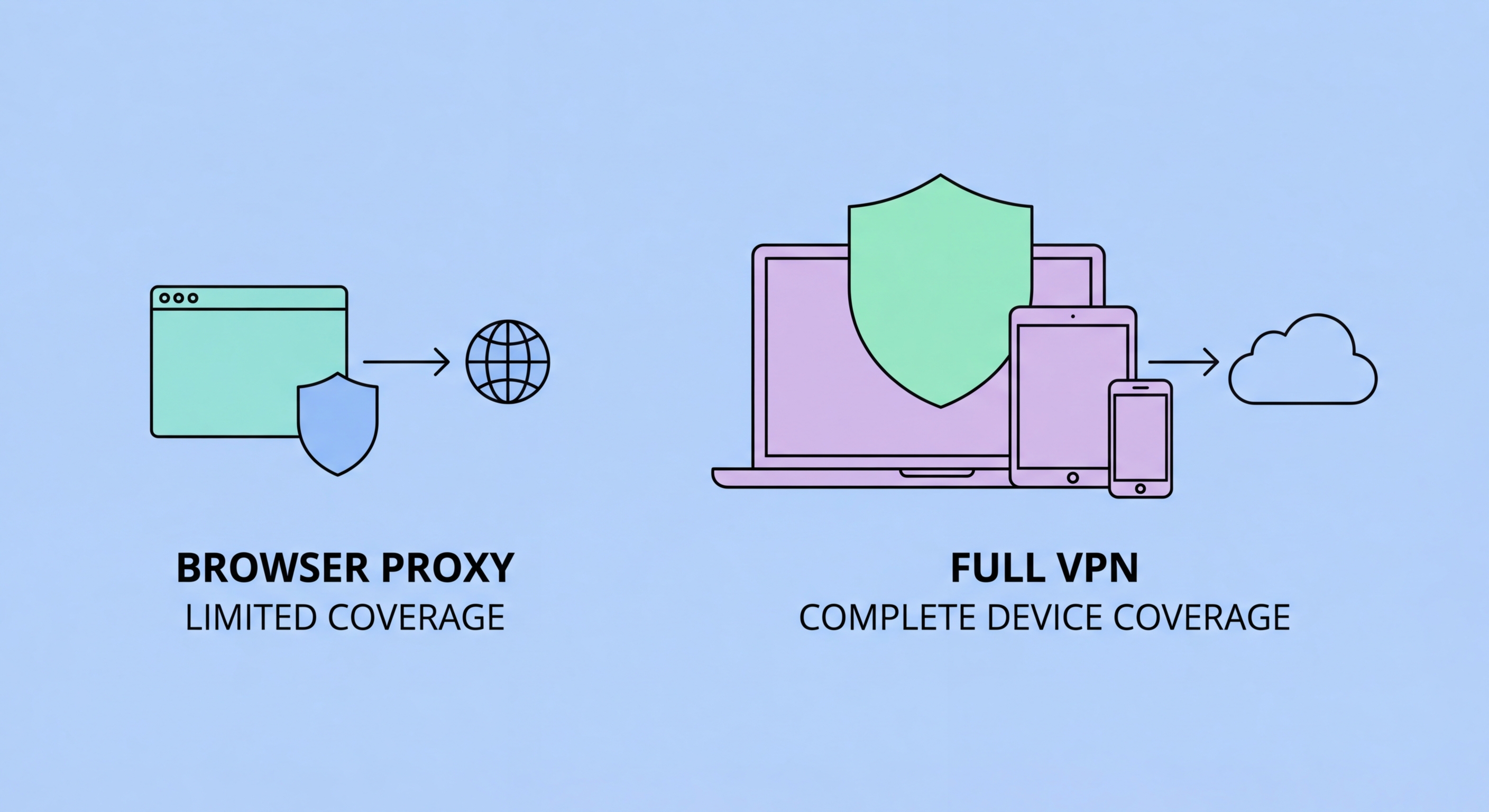
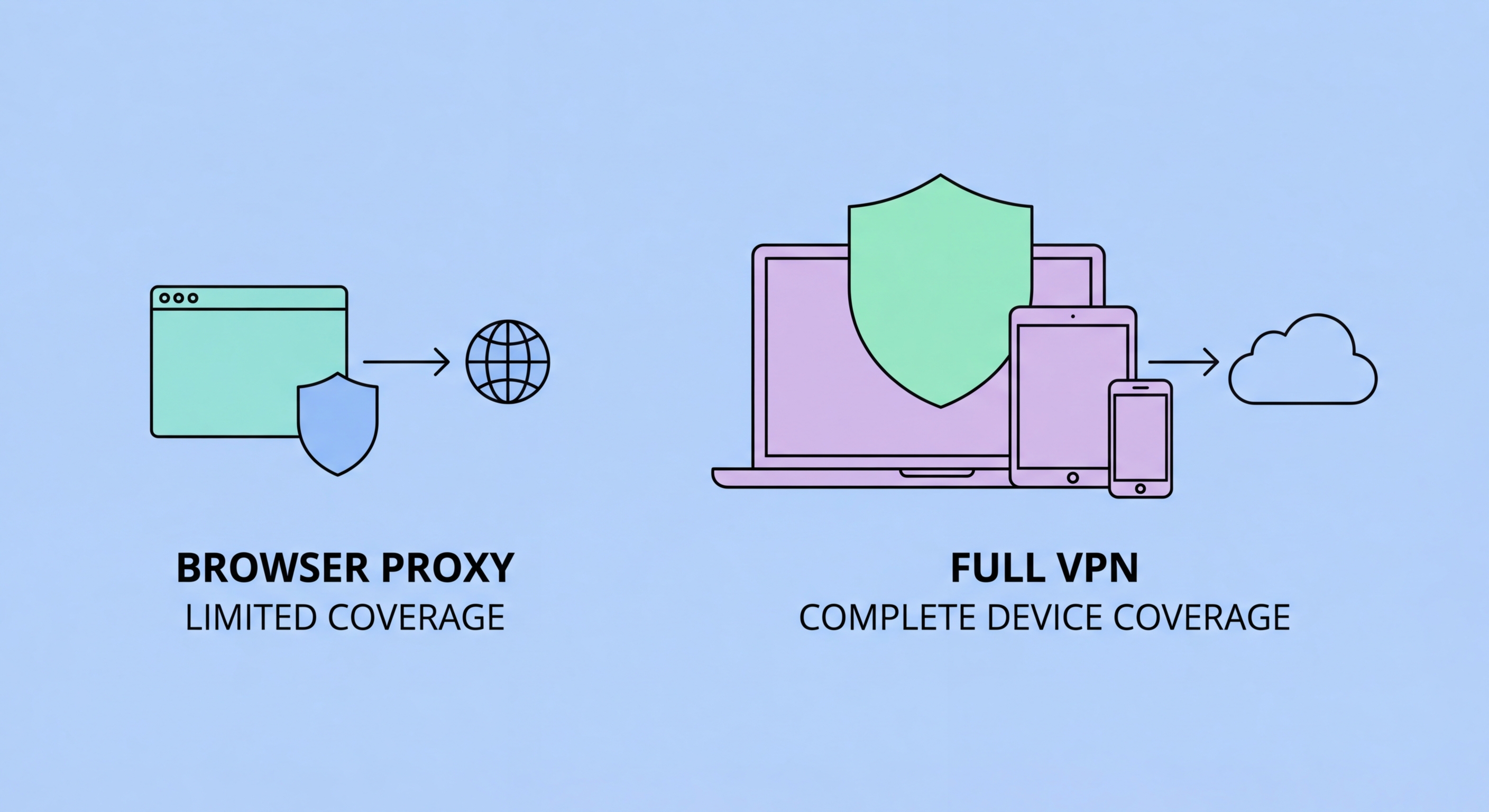
A browser proxy extension routes your browser's HTTP and HTTPS traffic through a proxy server, giving your browser connections a different IP address. The proxy acts as an intermediary between your browser and the websites you visit — websites see the proxy's IP address rather than yours. This is fundamentally a browser-only operation: only the traffic generated by the browser extension is routed through the proxy. Applications running on your computer outside the browser — messaging apps, email clients, system services, or other applications accessing the internet — continue to use your real IP address and are not affected by the proxy extension.
A full VPN creates an encrypted tunnel at the operating system level that captures all network traffic from all applications on your device. When a VPN is connected, every application — browser, email client, banking app, streaming app, messaging service — has its traffic routed through the VPN server. The operating system-level interception means no application can bypass the VPN without specific system-level privileges. VPN encryption also protects data in transit, not just the IP address — even if someone intercepts your VPN-tunnelled traffic, they cannot read the contents because it is encrypted. A browser proxy, by contrast, may or may not add encryption depending on the implementation.
The distinction matters significantly for privacy claims. If you use a browser proxy extension and then run a DNS leak test or IP check from a tool outside the browser (such as a system-level command), you will see your real IP address — because only browser traffic uses the proxy. All background processes, system updates, app syncing, and non-browser applications are sending traffic with your real IP to your ISP and the internet. For casual geo-unblocking of streaming content within a browser, a proxy extension may be sufficient. For privacy or security from ISP surveillance, a proxy extension provides much weaker protection than its marketing typically implies.

Free browser proxy extensions represent one of the highest-risk categories in the browser extension ecosystem. Unlike commercial VPN providers whose business model is subscription revenue, free proxy extensions need another revenue stream — and in many cases that revenue comes from selling users' browsing data to advertising networks and data brokers. The irony is that users install these extensions precisely to protect their privacy, while the extension is actively monetising their browsing history. Several high-profile free VPN extensions including Hola, Betternet, and numerous Chrome Web Store offerings have been documented collecting and selling user data.
Some free proxy extensions go further than data collection, using users' bandwidth and IP addresses to create peer-to-peer proxy networks that commercial customers pay to use. Hola VPN, one of the most downloaded browser extensions at its peak, was discovered to be selling users' bandwidth as exit nodes for its commercial counterpart, Luminati (now Bright Data). Users' home IP addresses and bandwidth were being rented to third parties — in some cases used for web scraping, in others for potentially illegal activity. Running arbitrary traffic through your IP address creates legal and reputational risks entirely unrelated to your own internet use.
Even free proxy extensions that are not actively malicious provide minimal security value. Without encryption, a proxy extension on an HTTP connection provides only IP masking, and the proxy server itself can see all your unencrypted traffic. The proxy provider knows exactly which sites you visit, linked to your real identity if you created an account, and linked to your real IP address which they logged before substituting it. The combination of weak protection, high data risk, and potential bandwidth exploitation makes free proxy extensions an option that should be avoided entirely — the only appropriate substitutes are either a paid VPN or a browser-native privacy browser with no proxy required.

Browser proxy extensions have limited legitimate use cases where their specific characteristics — browser-only, easy to toggle, fast to connect — provide value without creating significant risk. The most common legitimate use case is accessing geo-restricted content in a browser context where you do not have privacy concerns about the proxy provider seeing your traffic. For example, if you want to watch a streaming video available only in the UK and you trust the proxy provider's privacy policy, a browser proxy extension is a reasonable tool for that specific purpose — you are not concerned about ISP surveillance in this scenario, just IP-based geolocation.
Browser proxy extensions can also be acceptable for separating professional-looking browsing from your personal IP address for benign purposes like web scraping, market research, or competitive analysis, where the proxy provider's visibility into your browsing is not a concern because the browsing itself is not sensitive. Large enterprises sometimes use browser proxy settings for directing specific web traffic through corporate proxy servers for monitoring and compliance purposes — this is a technical use case where the proxy's visibility into traffic is the intended feature rather than a risk.
Browser proxy extensions should never be relied upon when the goal is genuine privacy from surveillance, protection of sensitive communications or identity, security on untrusted networks, or bypassing monitoring in high-risk environments. For these purposes, a full VPN — from a reputable paid provider with an audited no-logs policy — is the only appropriate tool. The browser-only nature, lack of encryption, and business model risks of free proxy extensions make them fundamentally inadequate for any serious privacy or security need. If you need to protect your identity and traffic comprehensively, a paid VPN is a modest monthly expense that delivers categorically stronger protection.

For the vast majority of Hong Hong Kong Users">Kong users seeking privacy protection — from ISP surveillance, from tracking on public WiFi, from corporate or government monitoring — a reputable paid VPN is the appropriate tool. Full VPNs from providers like ExpressVPN, NordVPN, Mullvad, and ProtonVPN cost between HK$30–90 per month and provide system-wide encrypted protection across all devices and applications. These providers have undergone independent security audits of their no-logs policies and have a track record of refusing to comply with data requests. The investment is modest relative to the comprehensive protection provided.
For users who specifically need to route only browser traffic through a different IP — perhaps to access a single streaming service or to test how a website appears from a different location — a paid browser proxy from a reputable provider (not a free extension) can be adequate. Some paid VPN providers also offer lightweight browser extensions that function as browser-only proxies, routing browser traffic through their servers without requiring the full VPN client to be running. These extensions from established VPN providers (ExpressVPN Lightway extension, NordVPN browser extension) are generally trustworthy in a way that standalone free proxy extensions are not.
The bottom line for Hong Kong users: if you want comprehensive privacy protection, invest in a paid VPN. If you want to change your IP address only in the browser for casual geo-unblocking, use a paid VPN provider's browser extension or their lightweight proxy mode — not a standalone free extension. Avoid all free browser proxy extensions for any privacy-sensitive purpose. The technical difference between a browser proxy and a full VPN is significant enough that conflating the two — as much proxy extension marketing does — creates a false sense of security that leaves users with substantially less protection than they believe they have.
