1QR Code Attack Types
How QR Code Scams Work in Hong Kong
QR code phishing — sometimes called "quishing" — exploits the widespread trust and adoption of QR codes in Hong Kong's daily life. Since COVID-19 normalised QR code scanning for restaurant menus, venue check-ins, and contactless payments, the technology has become deeply embedded in how people transact and access information. Scammers exploit this familiarity by placing fraudulent QR codes over legitimate ones, or creating entirely fake QR code displays in locations where scanning is expected.
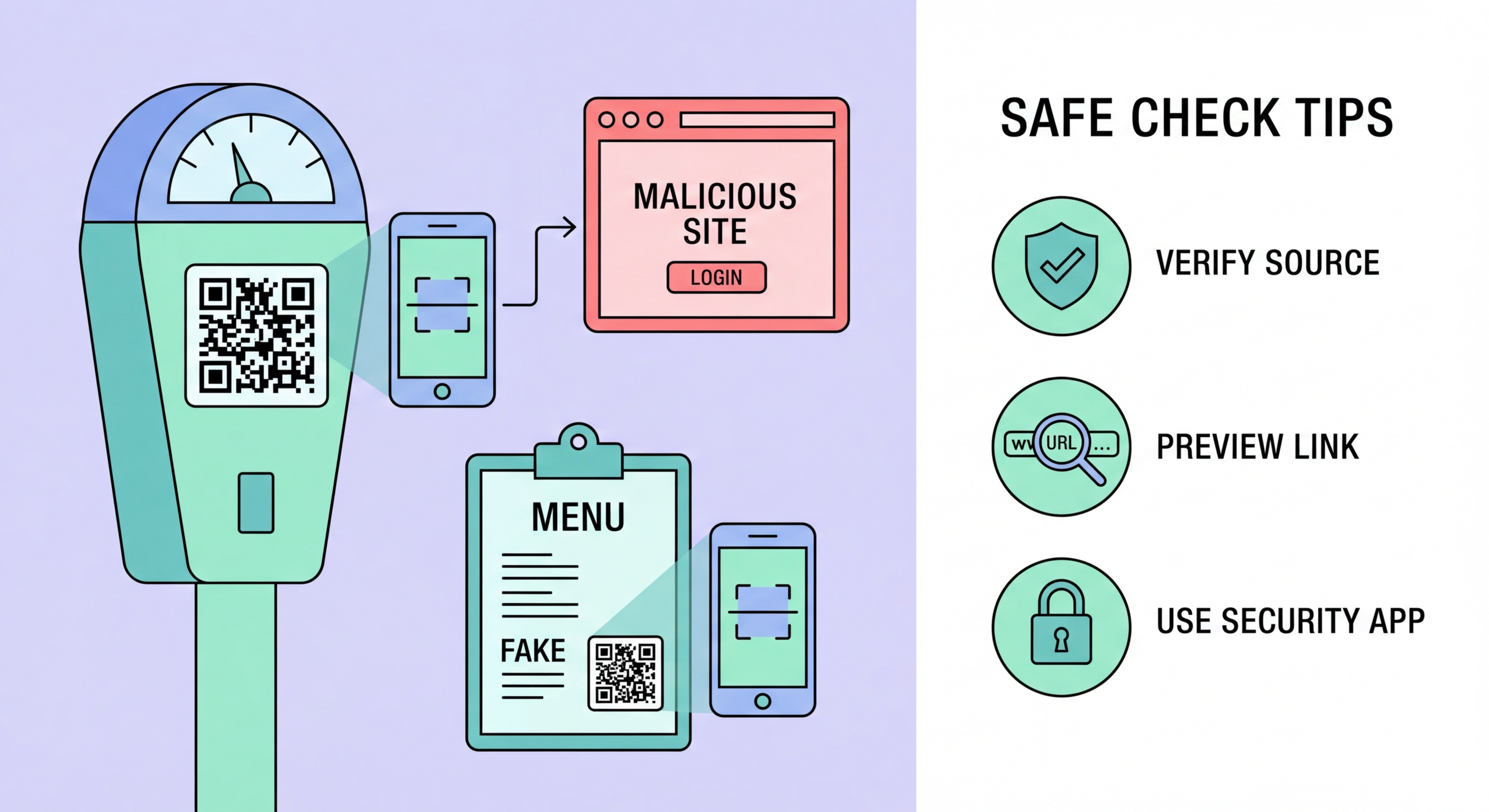
The most common QR code scam in Hong Kong involves physical replacement: a fraudulent QR code sticker is placed over a restaurant's legitimate menu QR code, a car park's payment QR code, or a business's cashless payment display. When scanned, the fraudulent code redirects to a phishing site or initiates an unexpected payment. The victim, expecting to access a menu or pay a parking fee, instead lands on a credential-harvesting site or makes a payment to a fraudulent recipient. Because scanning QR codes has become automatic and unquestioned, these attacks often succeed even against security-aware users.
Digital QR code scams appear in emails, messaging apps, and social media. Unlike physical replacement attacks, these fraudulent QR codes are designed to bypass email security filters — since QR codes are images rather than text links, they are not analysed by the same URL-scanning tools that would detect a malicious hyperlink. Scanning a QR code from an email or WhatsApp message carries the same risks as clicking a phishing link, but without the URL preview that might trigger caution.
- Physical replacement: Fraudulent stickers placed over legitimate QR codes in restaurants, car parks, and shops
- Credential harvesting: Scanned codes redirect to phishing sites that mimic legitimate services
- Payment hijacking: Fraudulent payment QR codes redirect payments to attackers' accounts
- Email quishing: QR codes in emails bypass URL-scanning security tools — same risk as clicking a phishing link
- WhatsApp quishing: QR code images in messages redirect to phishing sites when scanned
- HK prevalence: High QR code adoption in HK makes this attack particularly effective and frequently reported
Understanding the broader phishing threat →