3Ransomware: The Combined Threat
Ransomware in Hong Kong: The Phishing-Malware Combination at Its Most Damaging
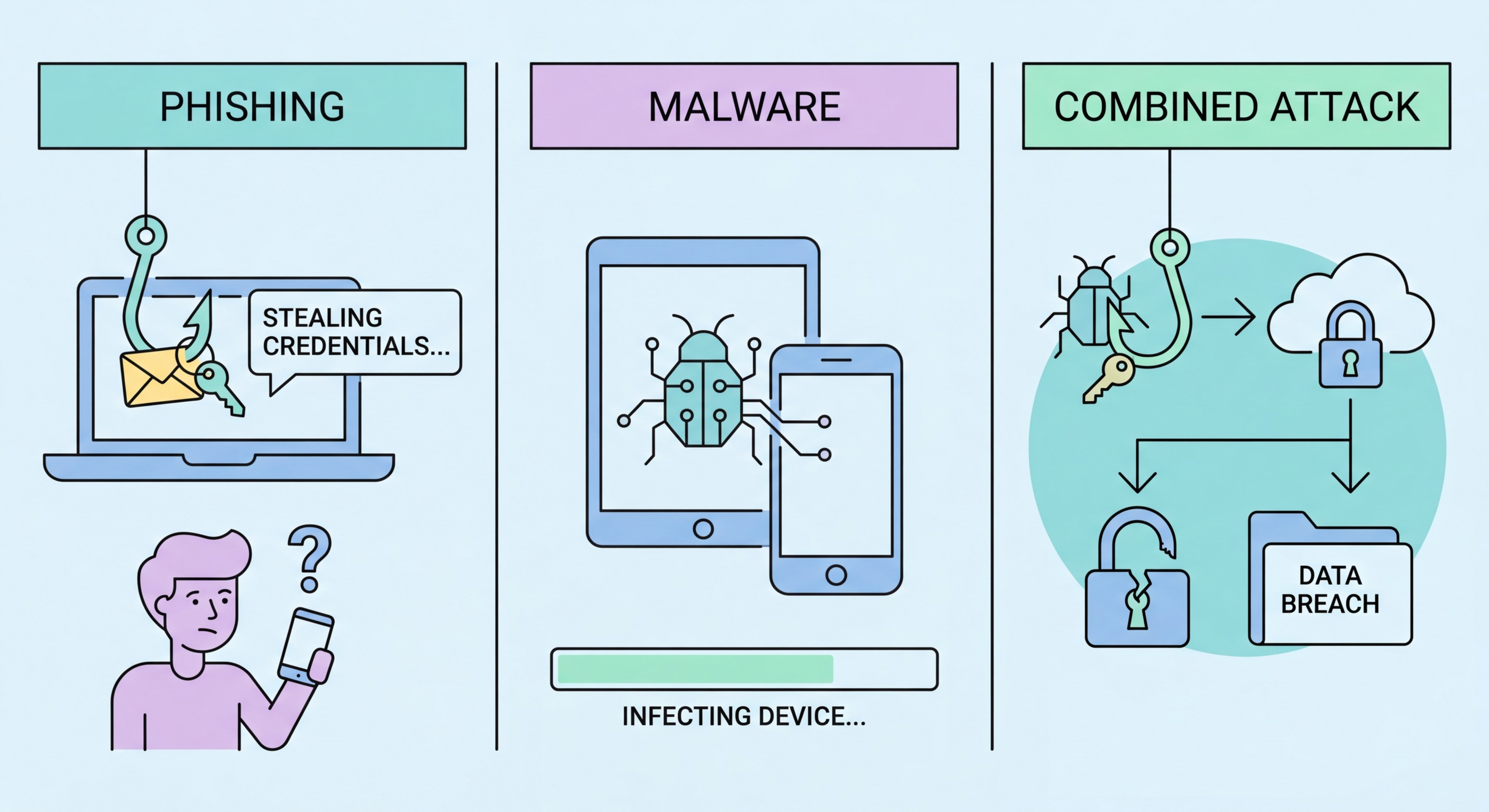
Ransomware is the most financially damaging category of malware-based attack and is almost universally delivered through phishing. A ransomware attack encrypts the victim's files and demands a cryptocurrency payment in exchange for the decryption key. For individuals, this means loss of personal files, photos, and documents. For businesses, it can mean complete operational paralysis — loss of access to all business systems, customer data, financial records, and operational infrastructure. Ransomware attacks on Hong Kong businesses have been documented across healthcare, logistics, professional services, and other sectors, with ransom demands typically in the tens of thousands to millions of US dollars and recovery periods of weeks to months.
The phishing component of a ransomware attack typically delivers an initial "dropper" — a small piece of malware that, once executed, downloads and installs the ransomware payload. The dropper may also install additional malware that exfiltrates data before encryption, enabling the attacker to threaten public release of sensitive data as additional leverage ("double extortion"). In some sophisticated ransomware operations, the dropper includes a remote access trojan that gives the attacker extended time to map the organisation's network, identify and compromise backup systems (to prevent recovery without paying the ransom), and identify the most valuable data before triggering the encryption. This reconnaissance phase may last weeks or months after the initial phishing delivery before the ransomware is deployed.
For Hong Kong businesses, ransomware preparedness involves both preventing the initial phishing delivery and implementing recovery controls that function even when ransomware successfully deploys. The latter includes: maintaining offline or cloud-backup copies of critical data that ransomware cannot reach (attackers specifically target and destroy online and network backups), testing restoration from backups regularly, maintaining an incident response plan that includes ransomware scenarios, and having relationships with cybersecurity incident response firms before an incident occurs. The HKCERT provides incident response guidance for Hong Kong organisations, and HKPF can provide law enforcement support including intelligence on the threat actor group behind specific ransomware attacks.
- Ransomware delivery: Almost universally phishing-delivered — email attachment or malicious link dropper
- Business impact: Complete operational paralysis — healthcare, logistics, professional services all affected in HK
- Double extortion: Data exfiltrated before encryption — threat of public release as additional ransom leverage
- Reconnaissance phase: Weeks to months between initial phishing delivery and ransomware deployment — backup targeting
- Offline backups: Critical recovery control — ransomware specifically targets network-accessible backups
- Incident response preparation: Plan and relationships before incident — HKCERT provides guidance for HK organisations
Technical tools that prevent phishing-delivered malware →