Network Security for Small Hong Kong Businesses
Practical network security for Hong Kong small businesses — covering firewall configuration, WiFi security, network segmentation, DNS filtering, and basic network monitoring without enterprise budgets.
Practical network security for Hong Kong small businesses — covering firewall configuration, WiFi security, network segmentation, DNS filtering, and basic network monitoring without enterprise budgets.
A firewall is the primary boundary control between your business network and the internet, inspecting traffic and enforcing rules about what is permitted to enter and leave. Every Hong Kong business with a network connection needs a firewall — not the basic NAT router provided by HKT, HKBN, or SmarTone as part of broadband packages, which provide minimal security functionality, but a dedicated security appliance or service capable of stateful packet inspection, application-layer filtering, and intrusion prevention. Consumer-grade routers lack the security controls, update cadence, and management capabilities needed for business use.
Business-grade firewalls appropriate for Hong Kong SMEs include the Sophos XG/XGS series, Fortinet FortiGate, WatchGuard Firebox, and Cisco Meraki MX — all of which provide unified threat management combining firewall, intrusion prevention, web filtering, and VPN in a single appliance with cloud-managed dashboards accessible to non-specialist administrators. For very small businesses, pfSense or OPNsense (open-source firewall platforms running on standard hardware) provide enterprise-class capabilities at hardware cost only, though they require more technical expertise to configure and maintain. Sophos Firewall Home Edition provides a free version limited to home/non-commercial use that allows SME IT administrators to build familiarity before commercial deployment.
Firewall rule configuration requires following the principle of least privilege: block everything by default and explicitly permit only what is required. The default rules in many business firewalls allow substantial outbound traffic that may not be necessary for your business — outbound DNS except to defined resolvers, outbound proxy connections, SMB traffic to the internet, and other traffic patterns that attackers exploit. Engaging an IT security professional for initial firewall rule review and configuration is worthwhile for most HK SMEs, followed by quarterly reviews as business needs change. Firewall logs should be retained and reviewed — particularly connection attempts to the firewall's management interface and unusual outbound connection patterns.

Business WiFi security is frequently underestimated as a network security risk. An unsecured or poorly secured WiFi network in a Hong Kong office building — where hundreds of other businesses share the same building — is a significant exposure. Wireless traffic captured by an attacker in the building or on the street below can expose business communications, credentials, and data. WiFi security configuration should be treated with the same rigour as firewall configuration. WPA3-Enterprise provides the strongest available WiFi security for business environments, authenticating each device individually through an 802.1X RADIUS server rather than sharing a single pre-shared key across all users.
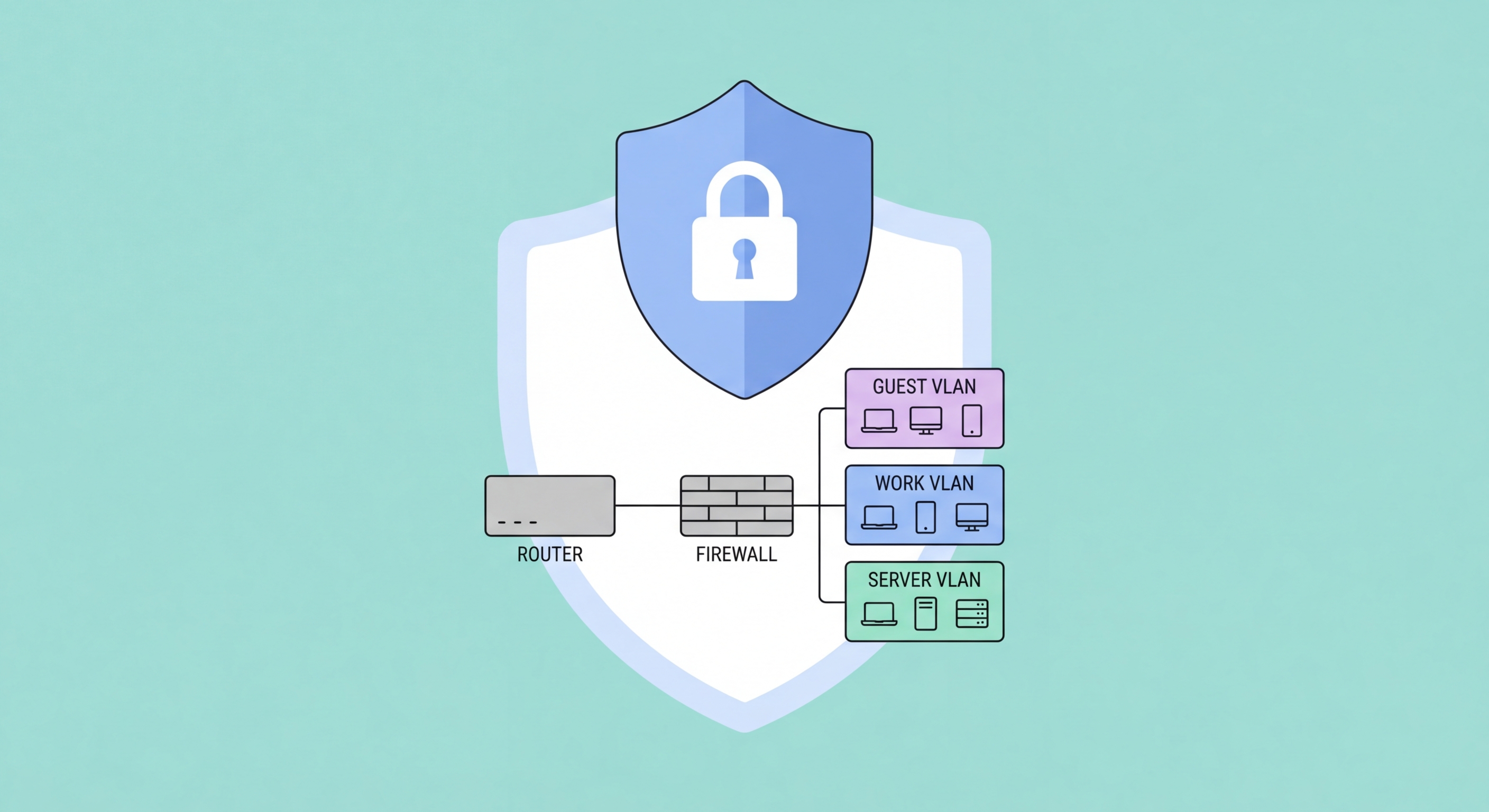
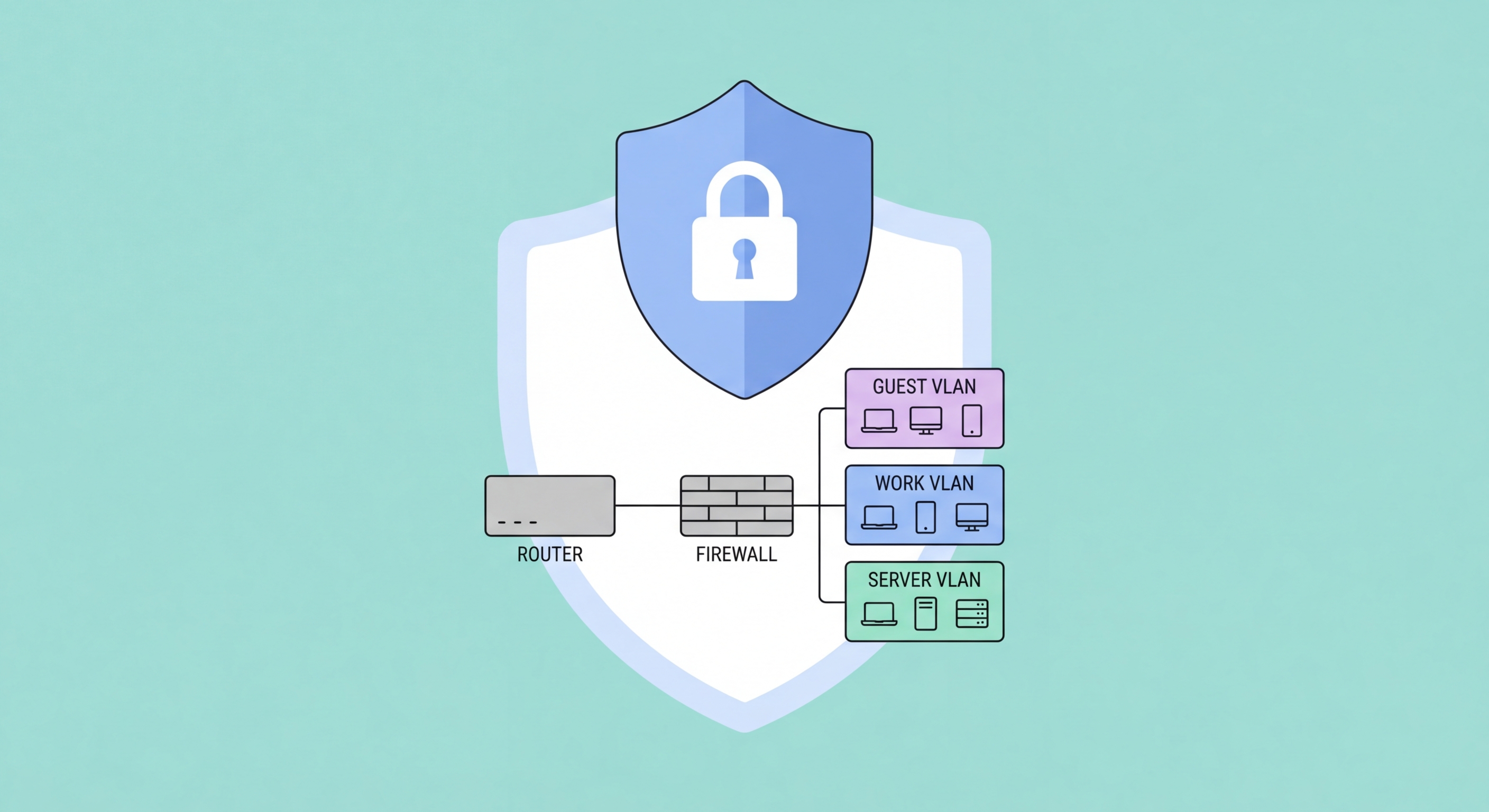
Network segmentation through VLAN separation is essential for business WiFi. Corporate devices — managed laptops and desktops — should connect to a corporate VLAN with access to internal systems and corporate cloud applications. Bring-your-own devices and mobile phones should connect to a separate BYOD VLAN with internet access but no path to internal servers. Guest WiFi for clients and visitors must be on a completely separate guest VLAN with internet-only access and no ability to reach either corporate or BYOD VLANs. Most business-grade wireless access points (Cisco Meraki, Ubiquiti UniFi, Aruba, and others) support this multi-SSID/multi-VLAN configuration and can be centrally managed. This segmentation limits the damage if a personal device or guest laptop on your WiFi is compromised — it cannot reach corporate resources.
WiFi management security — protecting the access point management interface and the wireless controller — prevents attackers who gain access to your network from modifying WiFi settings to create rogue access points or capture credentials. Change default management credentials on all access points immediately upon deployment. Disable remote management access from the internet. Use WPA3-Enterprise with certificate-based client authentication for highest-value corporate networks where pre-shared key compromise is a concern. Review connected devices regularly — IoT devices like printers, smart TVs, and building management systems should be on isolated VLANs rather than the corporate network, as they typically have poor security update histories.

Network segmentation divides a single flat network into isolated segments (VLANs or subnets) with controlled traffic paths between them. A flat network — where all devices can communicate with all other devices without restriction — means that a single compromised endpoint (a staff laptop infected with ransomware or a RAT) can immediately begin spreading to all other devices and servers on the network. Network segmentation forces traffic between segments through the firewall, where it can be inspected and controlled, limiting lateral movement and containing the blast radius of a compromise to the segment where it originated.
For Hong Kong SMEs, practical network segmentation typically involves separating: workstations (staff computers) from servers (file servers, application servers, databases) with firewall rules limiting what workstations can reach on the server network; WiFi devices from wired devices; POS systems and payment terminals on an isolated PCI-DSS compliant segment if you process card payments; IoT and building management devices on an isolated segment; and backup infrastructure on a segment inaccessible from workstations. This segmentation does not require expensive infrastructure — VLAN-capable managed switches (Cisco, Netgear, or HP/Aruba switches at SME price points) and a business firewall implementing inter-VLAN routing rules provide the required capability.
DNS filtering provides an additional network-level defence layer that stops malware communication and phishing site access regardless of endpoint security state. When a device on the network makes a DNS query for a known malicious domain — a ransomware command-and-control server, a phishing site, a malware distribution point — a DNS filtering service blocks the query before the connection is established. Cisco Umbrella, Cloudflare Gateway, and Palo Alto DNS Security provide business DNS filtering services. Cloudflare Gateway includes a free tier that provides significant protection for small businesses without cost. Configuring all DNS queries to route through a filtering service — by setting the firewall DHCP server to assign filtered DNS resolvers — provides coverage for all devices on the network without requiring per-device software installation.

Network monitoring — visibility into what is happening on your network — is the capability that converts security controls from passive defence into active detection. Without monitoring, a ransomware attacker can spend weeks on your network enumerating systems, stealing data, and destroying backups before deploying the encryption payload, with no indication to you that anything is wrong. With monitoring, unusual traffic patterns — a workstation connecting to dozens of servers it has never contacted before, large volumes of data being exfiltrated, connection attempts to known malicious IP addresses — trigger alerts that allow your team to investigate and contain the threat before it reaches its conclusion.
For SMEs without dedicated security operations, network monitoring does not require a full SIEM (Security Information and Event Management) deployment. Practical network monitoring for smaller HK businesses can be achieved through: firewall traffic logs reviewed weekly or forwarded to a managed security service, NetFlow analysis tools that provide traffic visibility without full packet capture (ManageEngine NetFlow Analyzer, PRTG Network Monitor), cloud-based network monitoring services that identify anomalous traffic patterns, and the security event logs built into Microsoft 365 and Google Workspace that identify unusual sign-in patterns and data access. The goal is not comprehensive monitoring of all traffic, but detection of the specific anomalous patterns that indicate active compromise.
Remote monitoring and management (RMM) tools — used by many IT service providers serving Hong Kong SMEs — provide infrastructure monitoring including device health, patch status, antivirus status, and connectivity monitoring from a centralised dashboard. If your business uses an IT managed service provider, ensure their monitoring scope includes security-relevant monitoring (failed authentication attempts, unusual process execution, new user account creation) in addition to infrastructure availability monitoring. For businesses managing their own IT, Atera, NinjaRMM, and ConnectWise Automate provide cloud-based RMM at SME price points with security monitoring capabilities that go beyond simple availability checks.
