1BYOD Risk Assessment
Understanding BYOD Security Risks for HK Businesses
Bring Your Own Device programmes — where employees use personal smartphones, tablets, and laptops for work purposes — are widespread among Hong Kong businesses, driven by operational convenience, cost savings on device procurement, and employee preference for their chosen devices. Many HK SMEs have defaulted into de facto BYOD without a formal policy simply because employees began using their iPhones for business email and WhatsApp for client communication. This unmanaged BYOD state — where personal devices access corporate data without any security controls — combines the risks of BYOD with none of its governance benefits, creating significant data exposure that most businesses are unaware of.
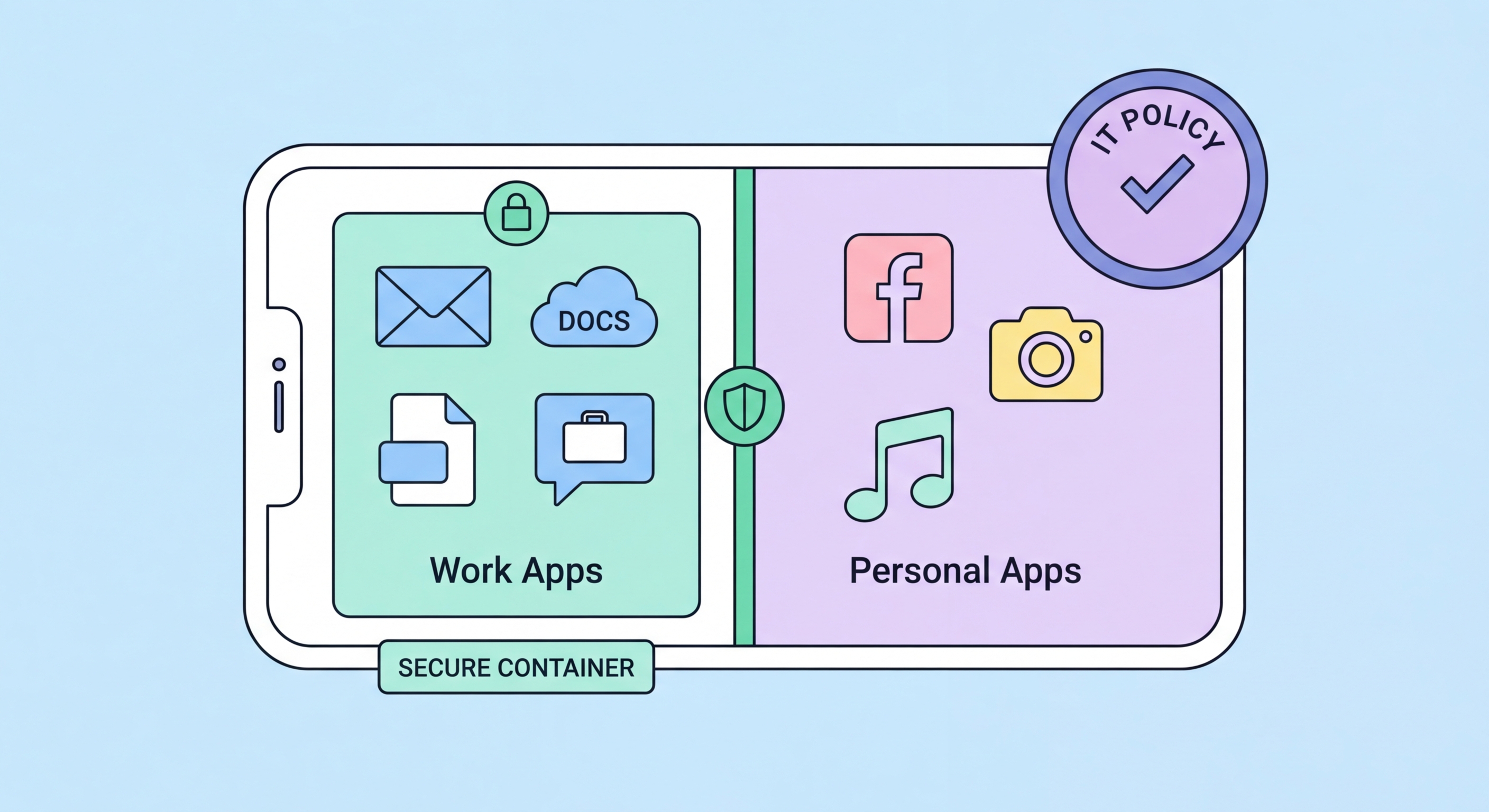
The security risks of unmanaged BYOD are substantial. Personal devices access corporate Microsoft 365 or Google Workspace accounts — downloading emails, attachments, and documents locally — without the organisation having any visibility into what data is stored on those devices. When an employee's personal phone is lost or stolen (or when they leave the company), that locally stored corporate data is outside the organisation's control. Personal devices may have weaker security configurations than corporate-managed devices: older iOS or Android versions not receiving security updates, third-party app stores with malicious applications, missing screen locks, or no encryption. The malware risk profile of a device used for personal gaming, social media, and web browsing is higher than a dedicated corporate device used only for work applications.
The PDPO implications of unmanaged BYOD are significant for Hong Kong businesses. When employee personal devices store customer personal data — in email, CRM applications, or downloaded files — those devices become repositories of personal data held by your business. PDPO Principle 4 requires appropriate technical and organisational measures to protect personal data. Personal devices used without security controls — no encryption, no remote wipe, no access control beyond a weak PIN — may not meet this standard. If a personal device containing customer data is lost, the resulting data breach may generate PCPD complaints and regulatory scrutiny of your data protection practices, even though the device was technically the employee's personal property.
- De facto BYOD risk: Many HK businesses are in an unmanaged BYOD state without realising it — personal devices accessing corporate cloud accounts create exposure without governance
- Local data storage risk: Corporate email, attachments, and CRM data downloaded to personal devices is outside organisational control when devices are lost, stolen, or employees depart
- Personal device malware risk: Devices used for personal apps, gaming, and social media have higher malware exposure than dedicated corporate devices
- PDPO personal data obligations: Personal devices storing customer personal data must meet PDPO Principle 4 security requirements — inadequate personal device security creates regulatory risk
- Screen lock and encryption: Personal devices without strong PINs and full-disk encryption provide minimal protection for corporate data — many employees use weak or no device locks
- App store risk: Android devices with sideloaded applications or third-party app stores create malware exposure absent from corporate-managed device environments