1Email Threat Landscape
Business Email Threats Facing Hong Kong Organisations
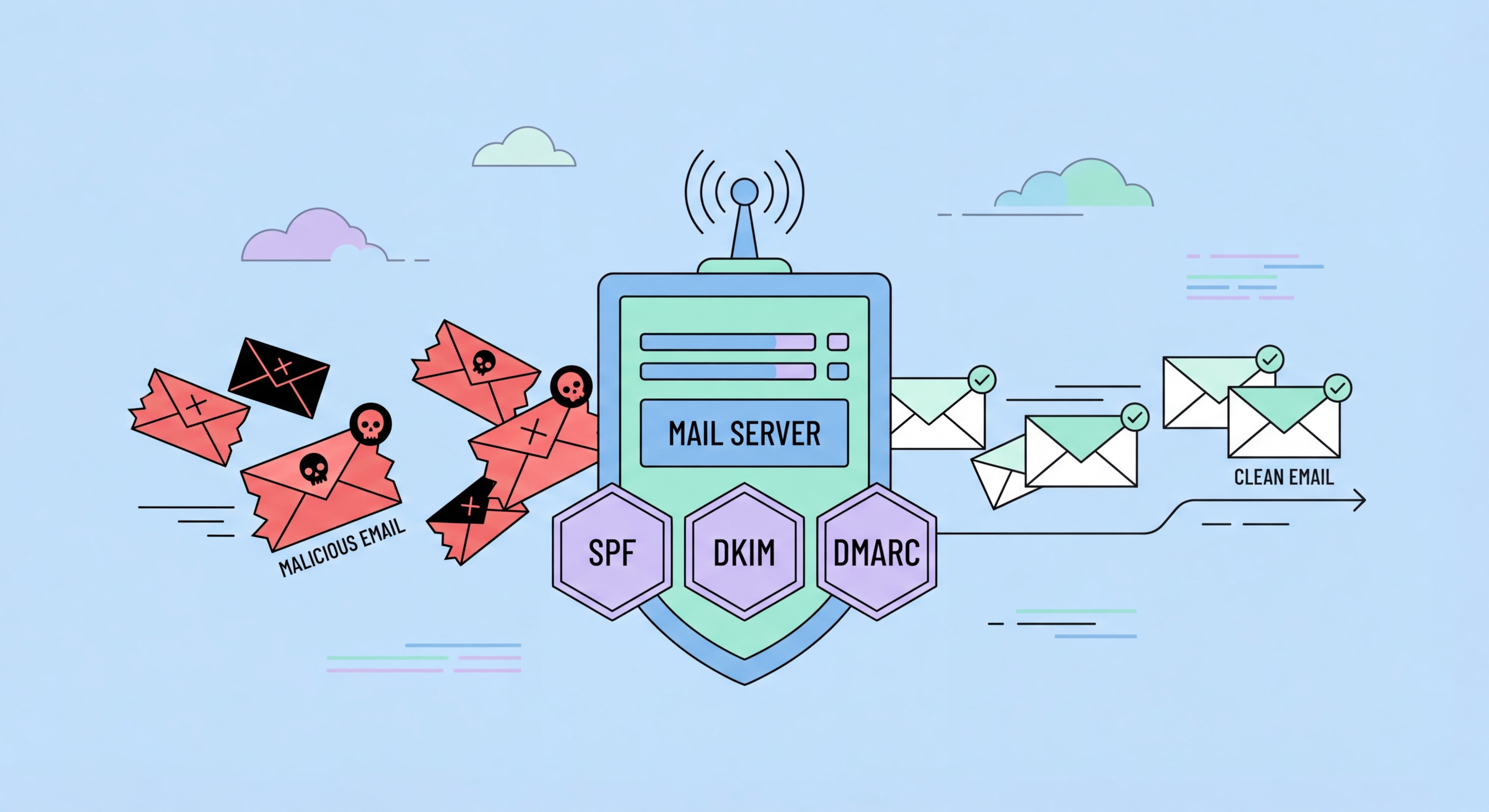
Email remains the most exploited attack vector against Hong Kong businesses. Despite advances in security technology, email's open architecture — designed for interoperability, not security — creates persistent vulnerabilities. Three primary email-based threats cause the majority of financial and operational damage to HK organisations: business email compromise (BEC), which exploits email to initiate fraudulent financial transactions; phishing, which uses email to steal credentials or deliver malware; and domain spoofing, which allows attackers to send emails appearing to come from your organisation's domain.
Business email compromise has become the highest-loss cybercrime category for Hong Kong businesses. Attackers either compromise a legitimate business email account (by stealing credentials or exploiting a vulnerability) or impersonate a business account through domain spoofing or lookalike domains. Once they have a convincing email identity, they manipulate recipients — typically accounts payable staff, CFOs, or payroll administrators — into initiating fraudulent wire transfers, changing vendor banking details, or redirecting payroll payments. The FBI's IC3 reports that BEC losses exceed all other cybercrime categories combined globally, and Hong Kong's dense commercial email environment makes it a high-value target.
Phishing targeting HK business email addresses delivers both credential-stealing pages (fake Microsoft 365 login pages that harvest corporate credentials) and malware payloads (ransomware, banking trojans, and RATs delivered through malicious attachments or links). Corporate email accounts are particularly valuable targets because they provide access to sensitive business communications, internal systems via SSO (Single Sign-On), and the social engineering leverage of a trusted business identity that can be used to attack your customers and partners.
- BEC as primary financial loss driver: Business email compromise causes the highest total losses of any cybercrime category against HK businesses
- Credential phishing targeting M365/Google: Fake Microsoft 365 and Google Workspace login pages harvest corporate credentials that provide broad organisational access
- Domain spoofing and lookalike domains: Attackers register domains similar to yours (companyname-hk.com) to send convincing fraudulent emails to your partners and customers
- Malicious attachment delivery: Phishing emails deliver ransomware and RATs through macro-enabled Office documents, PDFs, and executable attachments
- Supply chain email attacks: Compromised supplier or partner email accounts send convincing requests for payment detail changes targeting your accounts payable
- Internal email compromise lateral movement: Compromised employee email accounts are used to pivot within the organisation — trust in internal senders is weaponised