1Definition and Types
What Rootkits Are and the Different Types
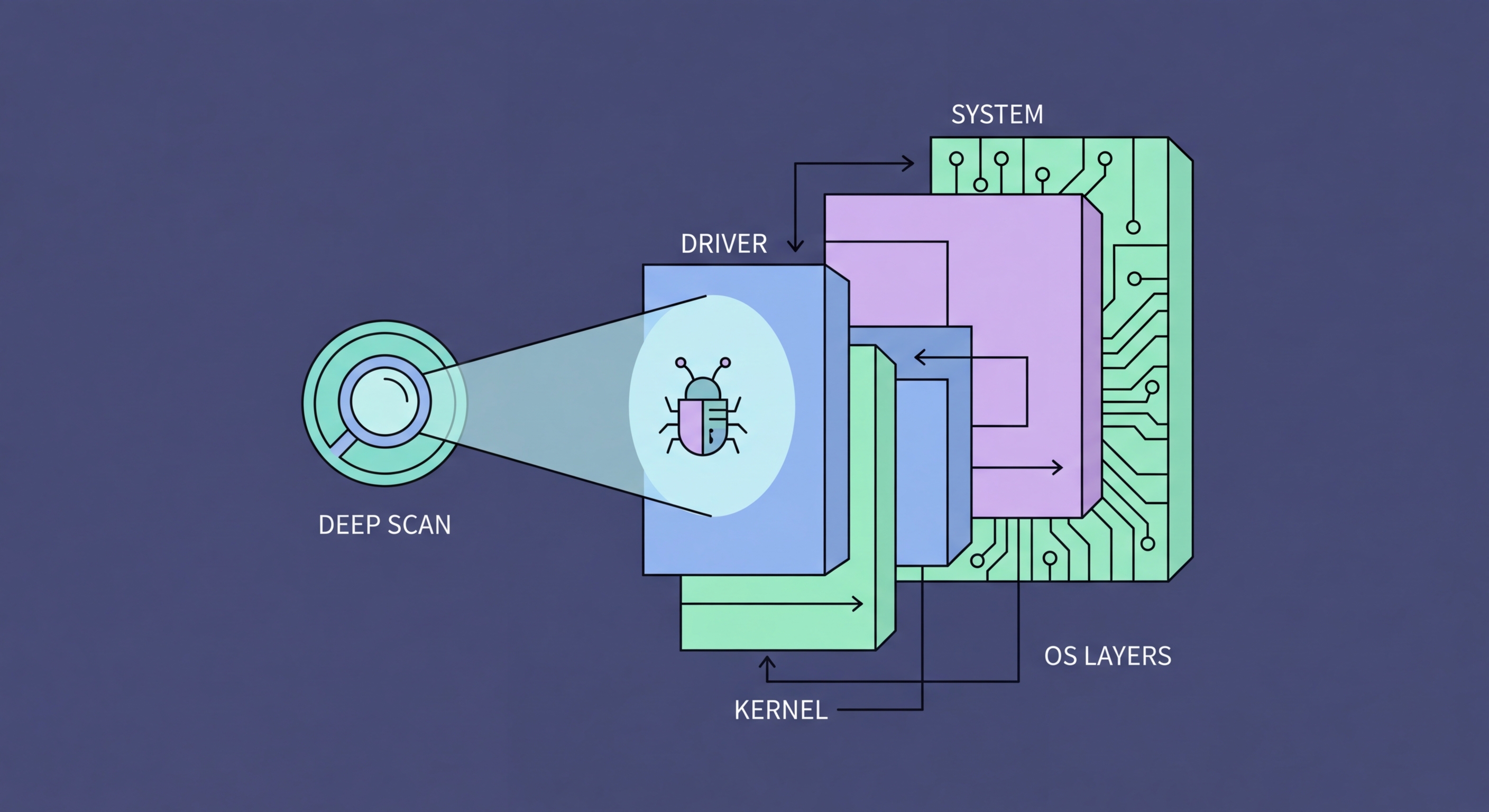
A rootkit is malware designed to gain privileged access to a computer system while actively concealing its presence from the operating system, security tools, and users. The name derives from Unix terminology — "root" being the highest-privilege system account, and "kit" referring to the collection of tools used to maintain that access. The defining characteristic of rootkits is not just what they do, but how they hide: rootkits modify the operating system's own reporting mechanisms so that the malware files, processes, registry entries, and network connections it creates are invisible to standard system queries. When you list running processes, the rootkit isn't shown. When you search for its files, they aren't returned.
Rootkits are classified by the privilege level at which they operate. User-mode rootkits operate at the application layer, intercepting API calls between applications and the OS kernel. They're easier to implement but also easier to detect. Kernel-mode rootkits — the more dangerous category — run at ring 0, the same privilege level as the operating system kernel itself, allowing them to modify kernel data structures directly and intercept any system call at the lowest level. Bootkits (boot-sector rootkits) infect the Master Boot Record or UEFI firmware, executing before the operating system loads — making them particularly difficult to remove as they operate before antivirus software even initialises. Hypervisor rootkits attempt to load the operating system as a virtual machine under a malicious hypervisor they install.
The practical impact of a rootkit infection goes beyond the rootkit itself. Rootkits are typically installed as part of a broader attack to maintain persistent, hidden access to a compromised system. Once a rootkit is in place, the attacker can install additional malware, steal credentials, use the system as part of a botnet, exfiltrate data, or conduct lateral movement through a network — all while the rootkit's concealment capabilities ensure detection is minimised. Some of the most significant advanced persistent threat (APT) campaigns attributed to nation-state actors have used sophisticated rootkits as core persistence mechanisms. In criminal malware, rootkits are often used to hide cryptocurrency mining software or botnet agents that provide ongoing value to the attacker.
- User-Mode Rootkit: Intercepts API calls at application layer — easier to implement and detect.
- Kernel-Mode Rootkit: Runs at OS ring 0 — modifies kernel data structures directly, hardest to detect.
- Bootkit: Infects MBR or UEFI — executes before OS loads, before antivirus initialises.
- Hypervisor Rootkit: Runs the OS as a VM under a malicious hypervisor — extremely rare and sophisticated.
- Concealment Function: Hides files, processes, registry keys, and network connections from OS queries.
- Persistence Platform: Primarily used to maintain hidden access and enable other malware installation.