2Layer 1: Antivirus and Browser Security
Building the Foundation: Antivirus and Safe Browsing Practices
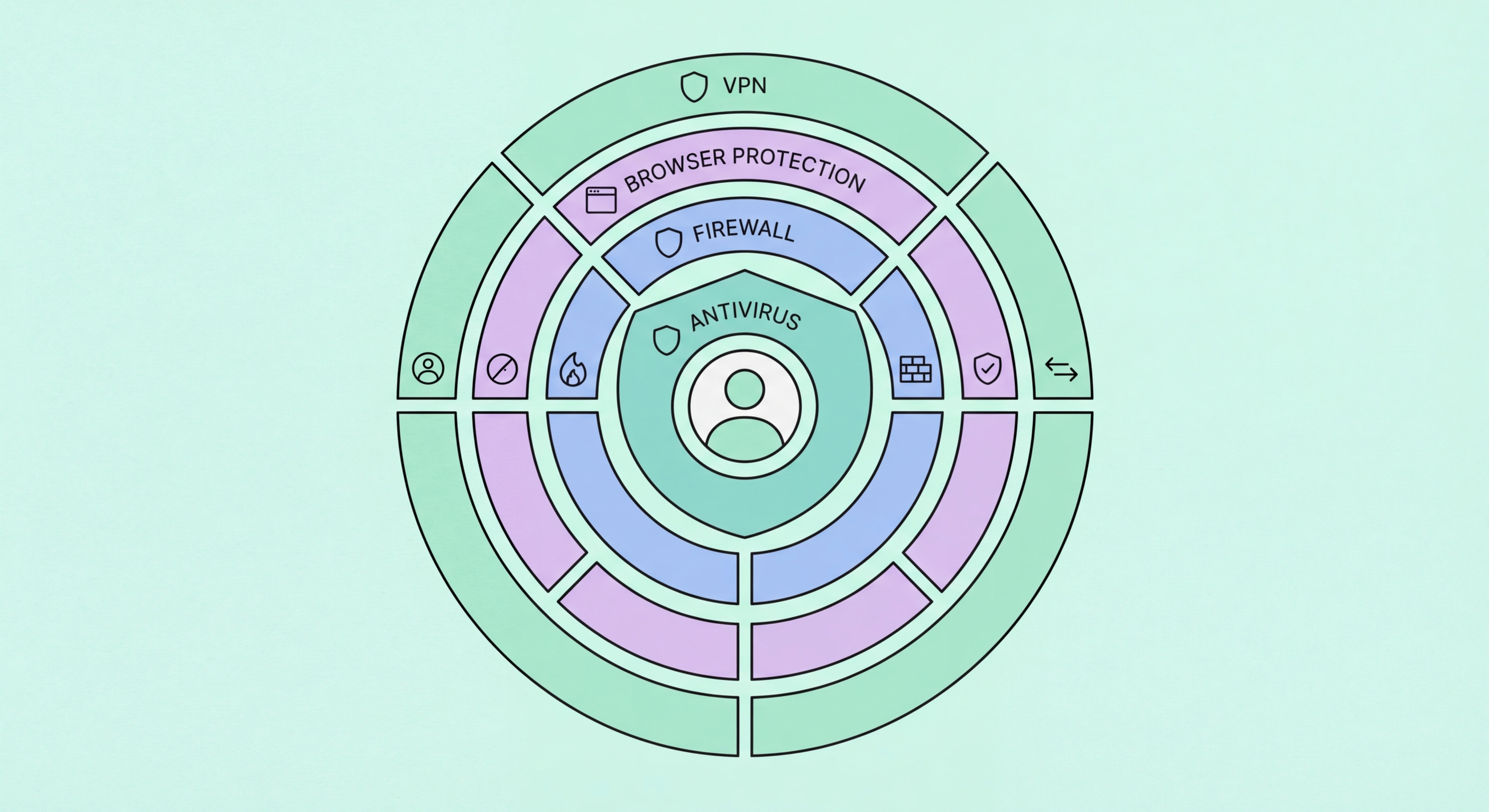
A quality antivirus with real-time protection is the foundational layer of a security stack. The combination of signature detection (for known malware), heuristic analysis (for malware variants), behavioural monitoring (for novel threats), and cloud threat intelligence (for newly discovered threats) provides broad-spectrum protection across the most common threat categories. For Hong for Hong Kong Users">Kong users, Bitdefender Total Security, Norton 360, or ESET Internet Security represent strong foundational choices based on independent testing performance. The key configuration requirements are: real-time protection always enabled, automatic definition updates active, and web protection configured to cover all browsers you use.
Safe browsing practices are the human component of the prevention layer and complement what antivirus handles technically. The most impactful safe browsing habits: verify URLs before clicking (particularly in emails and messages — hover over links to see the actual destination, which should match the claimed sender organisation); don't download software from unofficial sources (piracy sites, unofficial download portals, or sites offering "free" versions of paid software); keep browsers and browser plugins updated to the latest version; use a browser extension like uBlock Origin to block advertising networks that deliver malvertising; and treat any unexpected pop-up claiming your computer is infected as itself suspect — legitimate antivirus alerts come from your installed antivirus product, not from web browser pop-ups.
Browser extension hygiene is a frequently overlooked but important security practice. Browser extensions run with significant privileges — access to all page content you visit, the ability to read form inputs including passwords, and sometimes access to all browsing history. Malicious or compromised extensions have been used to steal banking credentials, session cookies, and other sensitive data from victims who installed them believing them to be legitimate productivity tools. Regularly audit installed extensions across every browser: Chrome Extensions (chrome://extensions), Firefox Add-ons (about:addons), Edge Extensions. Remove any extension you don't actively use, any you installed from an unfamiliar source, and any that request more permissions than their stated function requires. A screen capture extension doesn't need access to all browsing data; a weather widget doesn't need to read your browsing history.
- Foundation AV: Bitdefender, Norton, or ESET — real-time protection with web shield covering all browsers.
- URL Verification: Hover over links before clicking — actual destination must match claimed organisation.
- No Unofficial Software: Software from piracy sites is the primary trojan and malware delivery mechanism.
- uBlock Origin: Browser extension blocking malvertising networks — significant reduction in drive-by exposure.
- Extension Audit: Review and remove unused or excessive-permission browser extensions regularly.
- Pop-Up Scepticism: Browser pop-ups claiming infection are themselves scams — legitimate AV alerts come from installed software.