4Best Practice
How to Use Biometrics and Passwords Together for Maximum Security
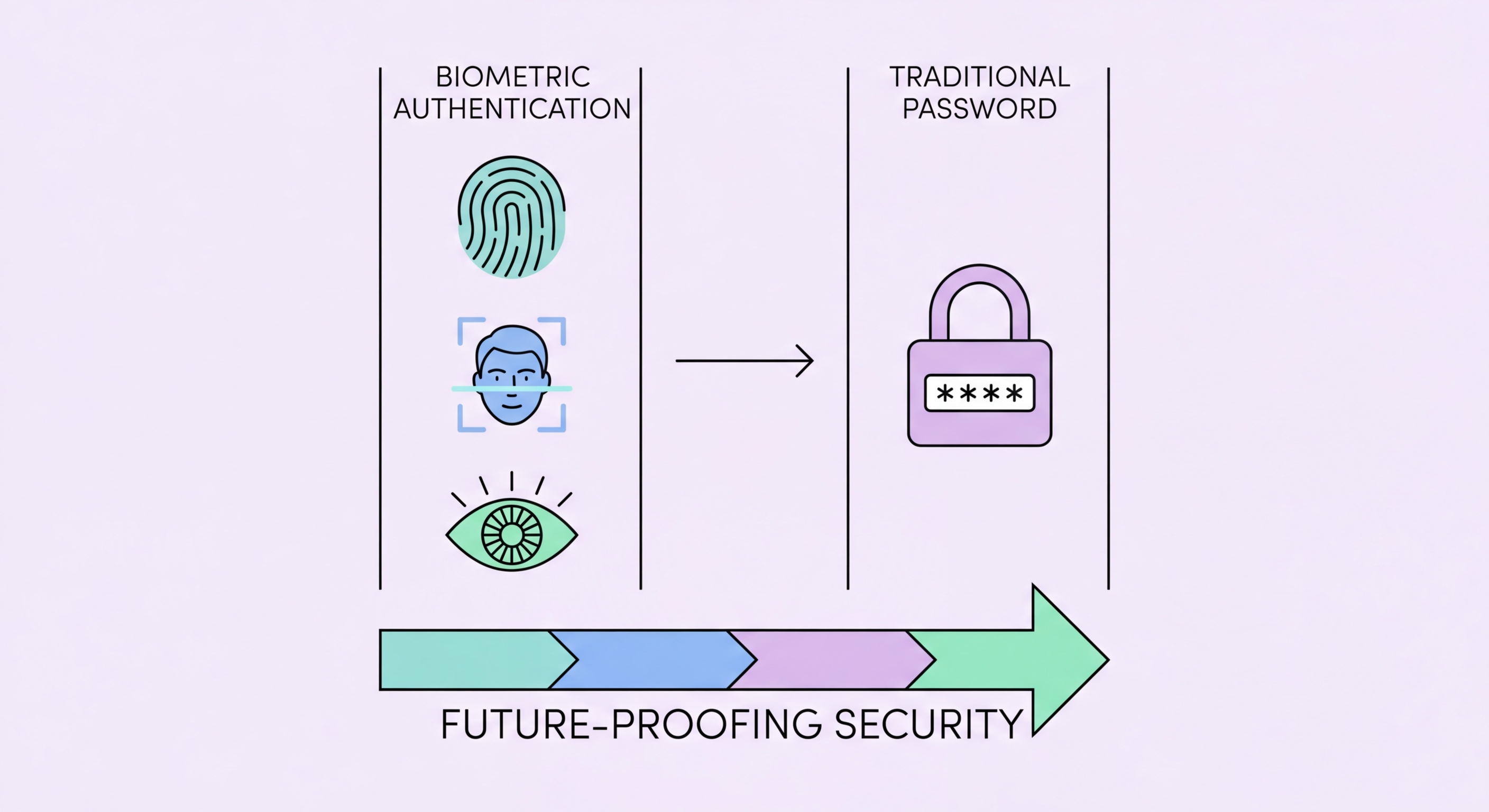
The current best practice is not to choose between biometrics and passwords but to use them together. For device unlock — smartphone, laptop, and tablet — enabling biometric unlock (Face ID, fingerprint) provides excellent daily usability while maintaining the password/PIN as a secure fallback for situations where biometrics cannot be used or should not be used. The device PIN or password should be strong enough to provide meaningful protection if the biometric is unavailable.
For app and website authentication, the emerging passkey standard (supported by Apple, Google, and Microsoft) uses the device's biometric as the user verification mechanism to release a cryptographic key — providing both the excellent usability of biometrics and the cryptographic security of public-key authentication. Passkeys are phishing-proof, not reusable across sites, and do not require server-side password storage. Where passkeys are available, use them — they represent the current gold standard in authentication security.
For high-security contexts — financial transactions, privileged administrative access, or situations involving legally sensitive information — consider treating biometrics as one factor in a multi-factor authentication scheme rather than a standalone authentication method. Financial apps in Hong Kong typically already implement this: Face ID or fingerprint confirms device presence and account ownership, but high-value transactions may additionally require a TOTP code or hardware token. This layered approach captures the usability benefits of biometrics while adding the security assurance of an additional factor.
- Layer biometrics with passwords: Biometric for daily convenience, strong PIN/password as fallback — use both together
- Strong PIN fallback: The PIN that unlocks your phone when biometrics fail should be 6+ digits or alphanumeric
- Use passkeys where available: The modern authentication standard combines biometric UX with cryptographic security
- MFA for high-value actions: Financial transactions and admin access should require biometric + additional factor
- Password manager with biometric unlock: Use Face ID/fingerprint to unlock your manager for daily use, master password for device changes
- Enable biometric on banking apps: All major HK banking apps support biometric login — enable it for daily security and convenience
The passwordless future — passkeys and beyond →