1Platform Myths
Platform-Specific Myths: Macs, iPhones, and Linux
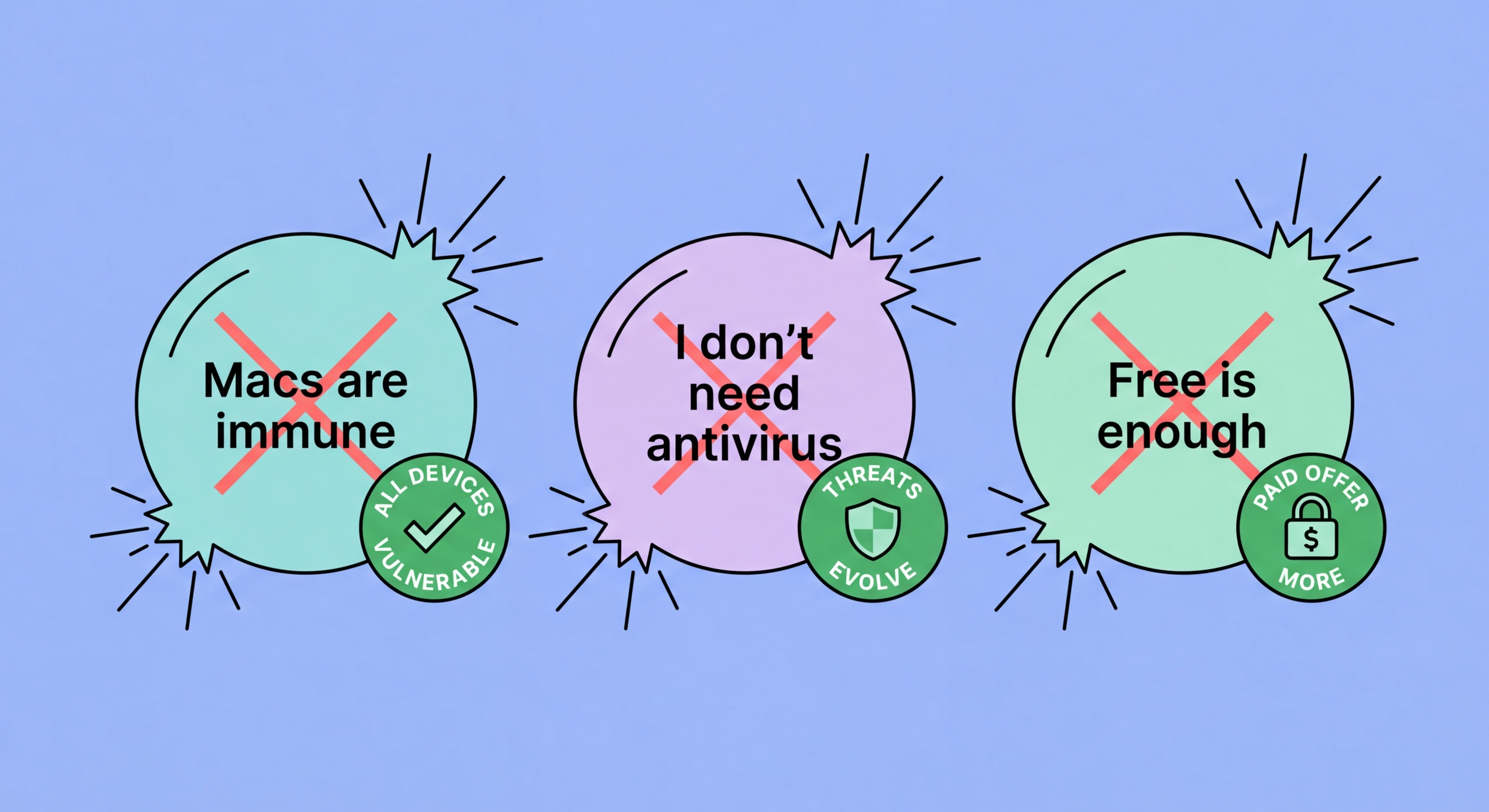
Myth: "Macs don't get viruses." This is one of the most persistently dangerous myths in consumer security. Macs absolutely do get malware — the Atomic Stealer (AMOS) info-stealer, Shlayer adware (historically the most prevalent Mac malware family), and a growing ecosystem of Mac-targeted threats demonstrate that macOS is a legitimate target for malware authors. The myth has a grain of historical truth: when Mac market share was much lower (5–10%), it made less economic sense for malware authors to invest in Mac-specific threats. As Mac market share has grown to 15–20% globally, and much higher in professional and creative sectors, the economic calculus changed. Mac-specific malware has grown substantially in sophistication and volume over the past five years. The appropriate response is to acknowledge the risk and choose appropriate protection — not to perpetuate a myth that leaves Mac users undefended.
Myth: "I use Linux, so I don't need antivirus." Linux is more resistant to casual malware than Windows for several reasons: smaller consumer market share, strong permission model, and open-source code that allows rapid community vulnerability identification. However, Linux is not immune to malware, and the server-focused nature of Linux makes it a high-value target for specific threats. Crypto-mining malware, rootkits, and backdoors specifically targeting Linux servers are well-documented. For desktop Linux users with low-risk browsing habits, antivirus may be genuinely unnecessary as a practical matter. But Linux servers handling sensitive data, web servers, or business-critical infrastructure should run antivirus scanning, intrusion detection, and file integrity monitoring — the same defence-in-depth principles apply regardless of OS.
Myth: "iPhones are completely secure and can't be hacked." iOS has a significantly stronger security architecture than Android, and typical iPhone users face dramatically lower risk of traditional malware infection. However, "can't be hacked" overstates iOS security. The Pegasus spyware — developed by Israeli company NSO Group — exploited zero-click iMessage vulnerabilities to achieve complete iPhone compromise with no user interaction required. Apple patches these vulnerabilities rapidly when discovered, which is why keeping iOS updated is critical, but the existence of Pegasus proves that iOS can be compromised at the highest level. For typical users, the more relevant iPhone threats are phishing and Apple ID compromise — neither of which is addressed by iOS's technical architecture and both of which require user education and account security practices.
- Mac Myth: Macs absolutely get malware — AMOS info-stealer and Shlayer adware are well-documented active threats.
- Mac Growth: Mac market share increase made it economically worthwhile to develop Mac-specific malware.
- Linux Reality: Linux servers are actively targeted by crypto-miners, rootkits, and backdoors despite OS advantages.
- iPhone Reality: Pegasus proves iOS can be completely compromised — "can't be hacked" is factually incorrect.
- iPhone Practical Threats: Phishing and Apple ID compromise are the realistic iPhone threats — both bypass iOS technical security.
- iOS Updates: Apple patches zero-day exploits rapidly — keeping iOS current is the key practical defence.