Account Takeover Fraud: How It Happens and How to Stop It
The mechanics behind Hong Kong bank account takeovers — from credential theft and SIM swapping to social engineering — and the defences that block each attack vector.
The mechanics behind Hong Kong bank account takeovers — from credential theft and SIM swapping to social engineering — and the defences that block each attack vector.
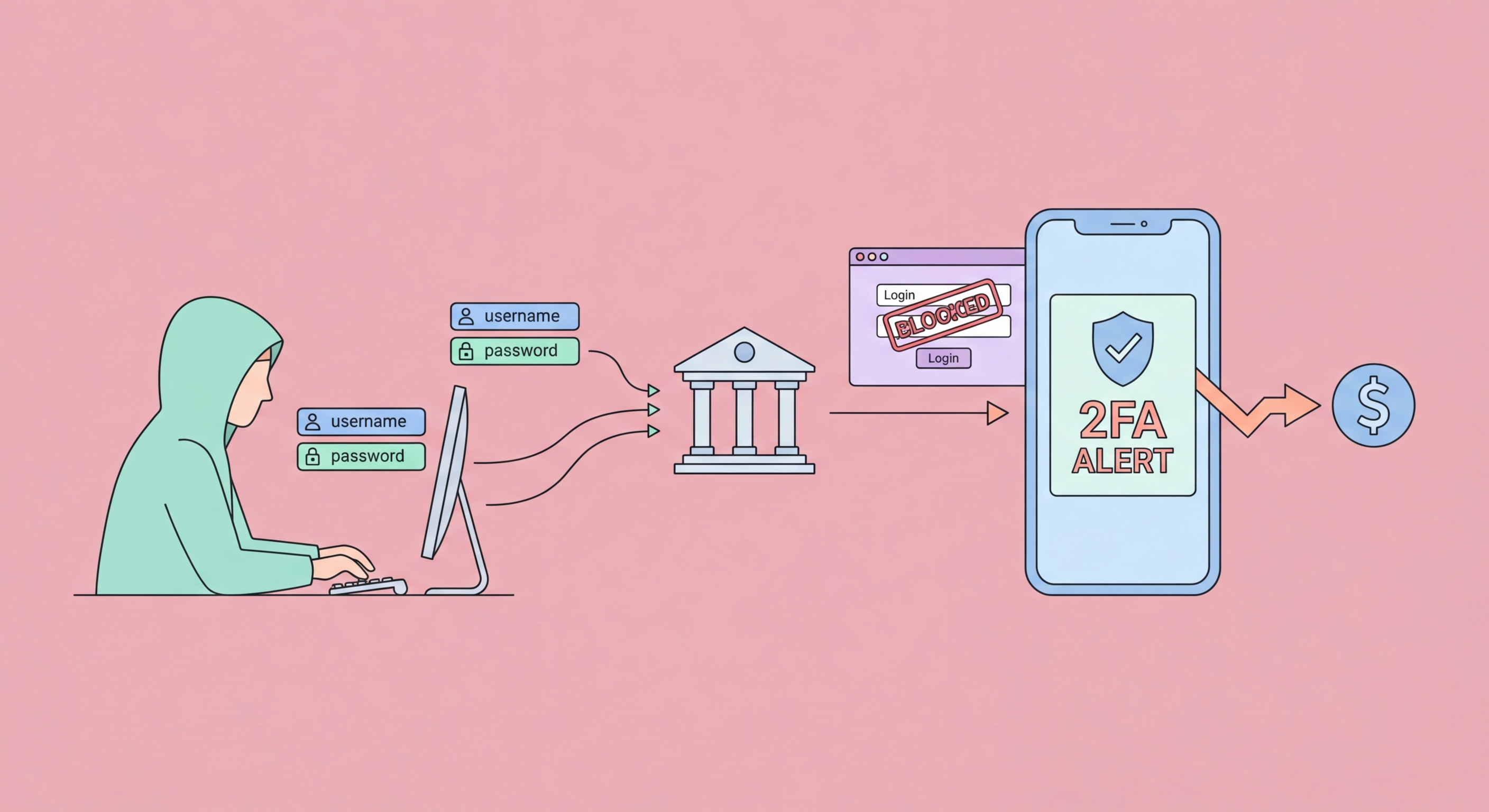
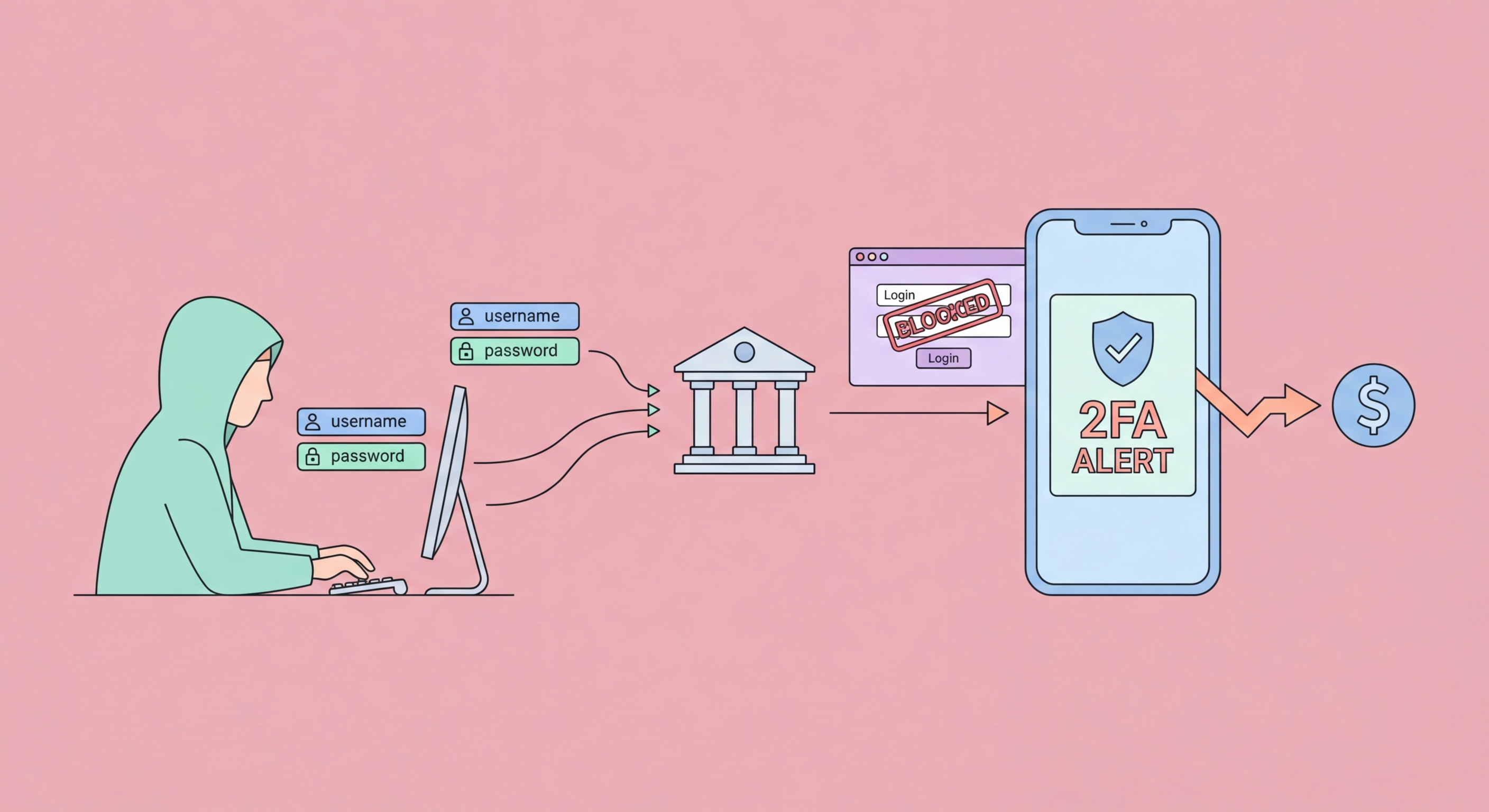
Account takeover fraud occurs when a fraudster gains sufficient control over your online banking credentials and authentication methods to conduct banking operations in your name. In Hong Kong, account takeovers originate through three primary pathways: credential compromise (obtaining your username and password), authentication bypass (circumventing the 2FA protecting the account), and social engineering (manipulating bank staff or you directly into granting access or making transfers). Many successful takeovers combine multiple pathways — credential theft followed by SIM swap to capture SMS OTPs is a common sequence.
Credential compromise is the most common entry point. Your banking credentials may be obtained through direct phishing (entering them on a fake bank website), through malware on your device (keyloggers, banking trojans), through credential stuffing using your username/password from an unrelated data breach, or through social engineering where a fraudster impersonating a bank employee requests your login details for "verification". The widespread practice of reusing passwords across services means that a single breach of any service — a retail website, an app, a forum — can expose your banking credentials if you use the same password there.
Once credentials are compromised, the attacker faces the challenge of bypassing 2FA. This is where SIM swapping becomes critical — by controlling your phone number, they receive all SMS OTPs sent to that number. Alternatively, real-time phishing kits automate OTP relay: when you enter your credentials on a phishing page, the kit immediately logs into your real bank, triggers an OTP sent to your genuine phone, and presents a fake "verification required" prompt that captures the code you enter and relays it to complete the fraudulent login. These real-time relay attacks render SMS OTP nearly ineffective against sophisticated phishing campaigns.

Preventing account takeover requires addressing each attack pathway independently. For credential security, a password manager generating unique, complex passwords for every service eliminates the credential stuffing risk — if every password is different, a breach at one site has no value for attacking your bank. Checking your email address at haveibeenpwned.com reveals whether your credentials have appeared in known data breaches — a result indicating prior breach should prompt immediate password changes for all affected services.
For 2FA hardening, migrating from SMS OTP to in-app authenticator tokens provided by your bank removes SIM swap vulnerability from your banking authentication chain. This is the single highest-impact security improvement available to most HK banking customers and can typically be done independently through your bank's mobile app settings in under five minutes. Where in-app authentication is not available, using a separate SIM card — one not linked to your identity in any public record — exclusively for banking SMS OTPs is a partial mitigation for SIM swap risk.
Device security closes the malware pathway. Running reputable antivirus software on all devices used for banking, keeping operating systems and apps updated to receive security patches, avoiding installation of apps from sources outside official app stores, and being extremely conservative about granting permissions to newly installed apps all reduce the risk of banking trojans gaining a foothold. Dedicated device separation — using one device exclusively for banking and financial management, with no social apps, games, or general browsing — represents the strongest device-level protection for users with significant holdings.

Social engineering account takeover bypasses technical security entirely by manipulating human beings — you, bank staff, or your mobile operator's customer service agents. Fraudsters invest significant effort in these attacks because they can succeed regardless of how strong your passwords and 2FA are. The most common social engineering takeover attempts in Hong Kong involve impersonating bank staff calling to "verify" suspicious activity, impersonating your employer or IT department requesting access to banking facilities, or fabricating emergencies that require urgent account actions.
The critical defensive principle against all social engineering attacks is independent verification. If someone contacts you claiming to be your bank and requests any information or action, do not comply during that call or communication. Instead, hang up and call your bank's official published number independently. Check the number on the back of your card or your bank's official website — not a number provided in the call or message. This simple procedure defeats telephone impersonation attacks entirely, because the fraudster cannot intercept a call you initiate to the real bank's number.
Vishing attacks — voice phishing — are particularly effective because fraudsters can spoof caller ID to display your bank's genuine phone number. Do not trust the number displayed on your phone screen as authentication of the caller's identity. Genuine bank staff will never need to call you and ask for your full password, PIN, or OTP — any caller making these requests is fraudulent regardless of what number appears on your screen. Banks occasionally do call customers about suspicious activity but will identify themselves, never request sensitive credentials, and will never object to you hanging up to call back on the official number.

Early detection is the key to minimising losses from account takeover. The warning signs are usually present before significant damage occurs: unexpected SMS OTPs arriving when you have not attempted to log in, login notifications for access from unfamiliar devices or locations, unexpected transaction notifications, email notifications of security settings changes (password, device registration, registered phone number), or your mobile phone unexpectedly losing all network connectivity (indicating a SIM swap in progress). Any of these signals requires immediate action.
If you suspect an account takeover is in progress, your priority actions in order are: immediately lock or freeze the account via your bank's app emergency lock feature (available in most HK bank apps under Settings > Security or as an emergency widget), change your banking password immediately from a different device, call your bank's 24-hour fraud hotline from a different phone, and contact your mobile operator if you suspect a SIM swap. Acting within minutes rather than hours can determine whether fraudsters complete transfers or are stopped before your funds are drained.
After immediate containment, conduct a systematic review. Check your bank account for any: new payees or beneficiaries added, standing orders modified or added, FPS aliases changed, contact details (email, phone) updated, and any transaction activity in the period before you detected the compromise. Report all findings to your bank and police. Change passwords for any other service that shares the compromised password or email account. Check your email account for suspicious activity, as email is often the gateway to banking account recovery — an attacker who can access your email can often trigger password resets at your bank.
