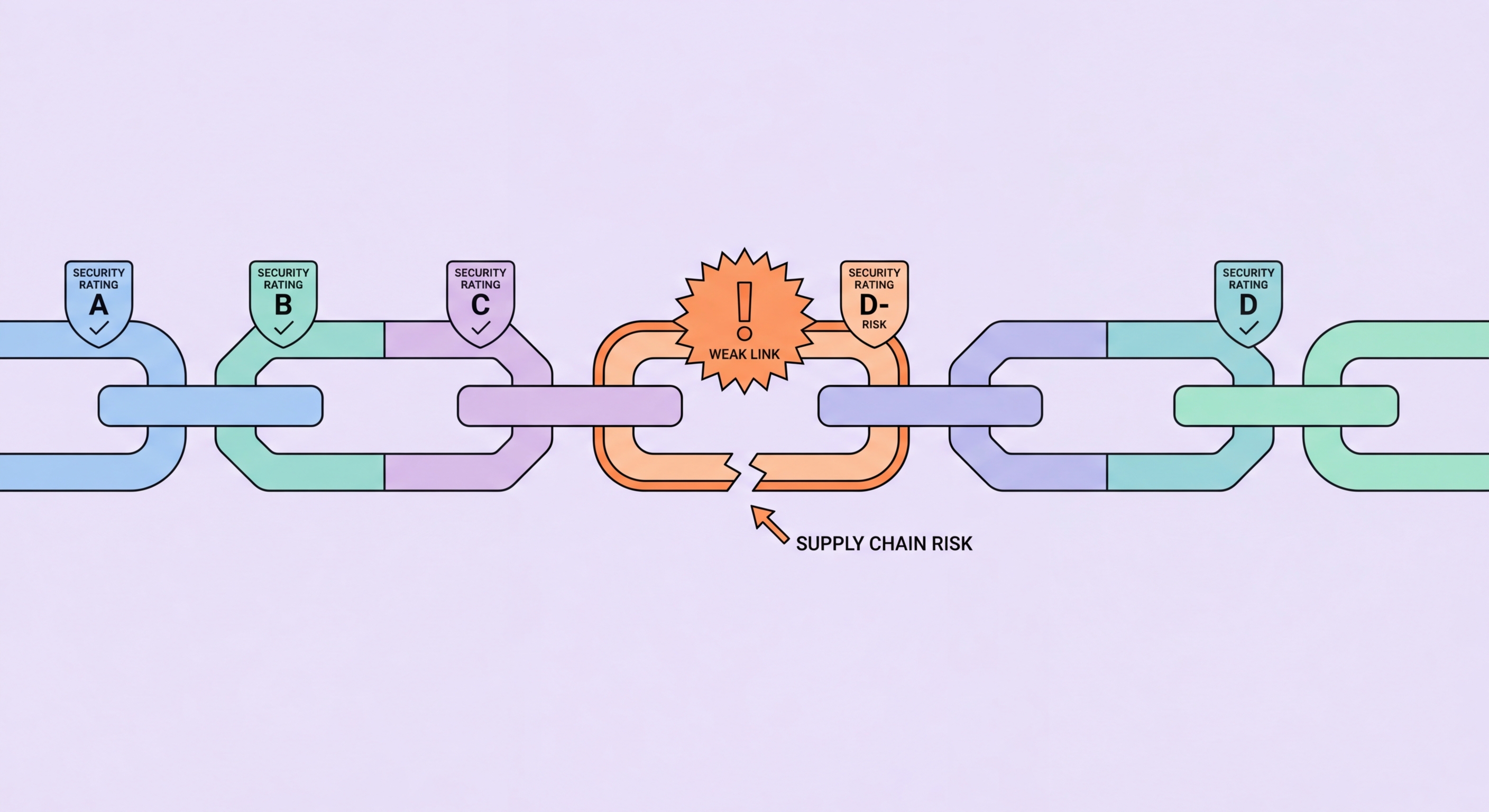
1Supply Chain Risk
Understanding Supply Chain Cybersecurity Risk for HK Businesses
Supply chain cybersecurity risk arises when your business's security posture is undermined through a third-party vendor or supplier who has access to your systems, networks, or data. High-profile supply chain attacks — including SolarWinds, Kaseya VSA, and 3CX — demonstrated that sophisticated attackers compromise widely-used software vendors and managed service providers to gain simultaneous access to thousands of downstream customers. For Hong Kong businesses, supply chain risk is particularly relevant given the region's concentration of financial services, professional services, and trading companies that rely on extensive webs of technology vendors, IT managed service providers, and outsourced business function providers.
The third-party risk landscape for a typical Hong Kong SME includes: IT managed service providers with privileged administrative access to your servers and endpoints, cloud services that store or process your customer data (accounting platforms, HR systems, CRM), business software vendors whose products are installed on your network, professional service firms (accountants, lawyers, consultants) with access to sensitive business data, and logistics or supply chain partners connected to your business systems. Each of these relationships represents a potential pathway for attackers to reach your business. A breach at your IT MSP can expose your systems through the same administrative tools used for legitimate maintenance. A breach at your accounting SaaS vendor can expose your financial data and customer records without your systems being directly compromised.
Hong Kong's PDPO imposes direct obligations on data users (your business) for the security of personal data even when that data is processed by a third party. A data breach at a processor you engaged — your CRM vendor, your HR system provider, your cloud accountant — can result in PCPD complaints and investigations directed at your business as the data user, even though the breach occurred at the processor. Principle 4 of the PDPO requires data users to use contractual means and other practicable steps to prevent personal data held by processors from unauthorised or accidental access. This creates a legal imperative, not merely a best practice, for supply chain security management by HK businesses.
- IT MSP risk: Your IT managed service provider typically has privileged access to all your systems — a breach at your MSP is effectively a breach of your organisation
- SaaS vendor risk: Cloud applications holding customer data, financial records, or employee data represent significant supply chain risk if the vendor is breached
- PDPO data processor obligations: PDPO Principle 4 requires contractual protections for personal data held by processors — you are legally responsible for your vendor's data security
- Software supply chain: Software installed on your systems from vendors with poor security practices can introduce vulnerabilities or backdoors that compromise your network
- Payment processor security: Payment processors and POS vendors with access to your payment infrastructure require careful security assessment
- Cross-border data transfers: Vendors who process HK customer data in jurisdictions outside Hong Kong create additional PDPO obligations for cross-border data transfer due diligence