1Understanding Ransomware
How Modern Ransomware Attacks Work Against HK Businesses
Modern ransomware attacks against Hong Kong businesses bear little resemblance to the opportunistic, spray-and-pray ransomware of a decade ago. Today's ransomware operations are sophisticated criminal enterprises operating Ransomware-as-a-Service (RaaS) platforms, where developers create the ransomware and affiliates conduct targeted attacks in exchange for a percentage of ransom payments. LockBit, BlackCat/ALPHV, Cl0p, and their successors specifically target businesses in Hong Kong's financial, professional services, and logistics sectors because these industries can afford to pay substantial ransoms and are operationally dependent on continuous data access. The HKPF CSTCB has reported ransomware as among the most financially damaging cybercrime categories affecting HK businesses.
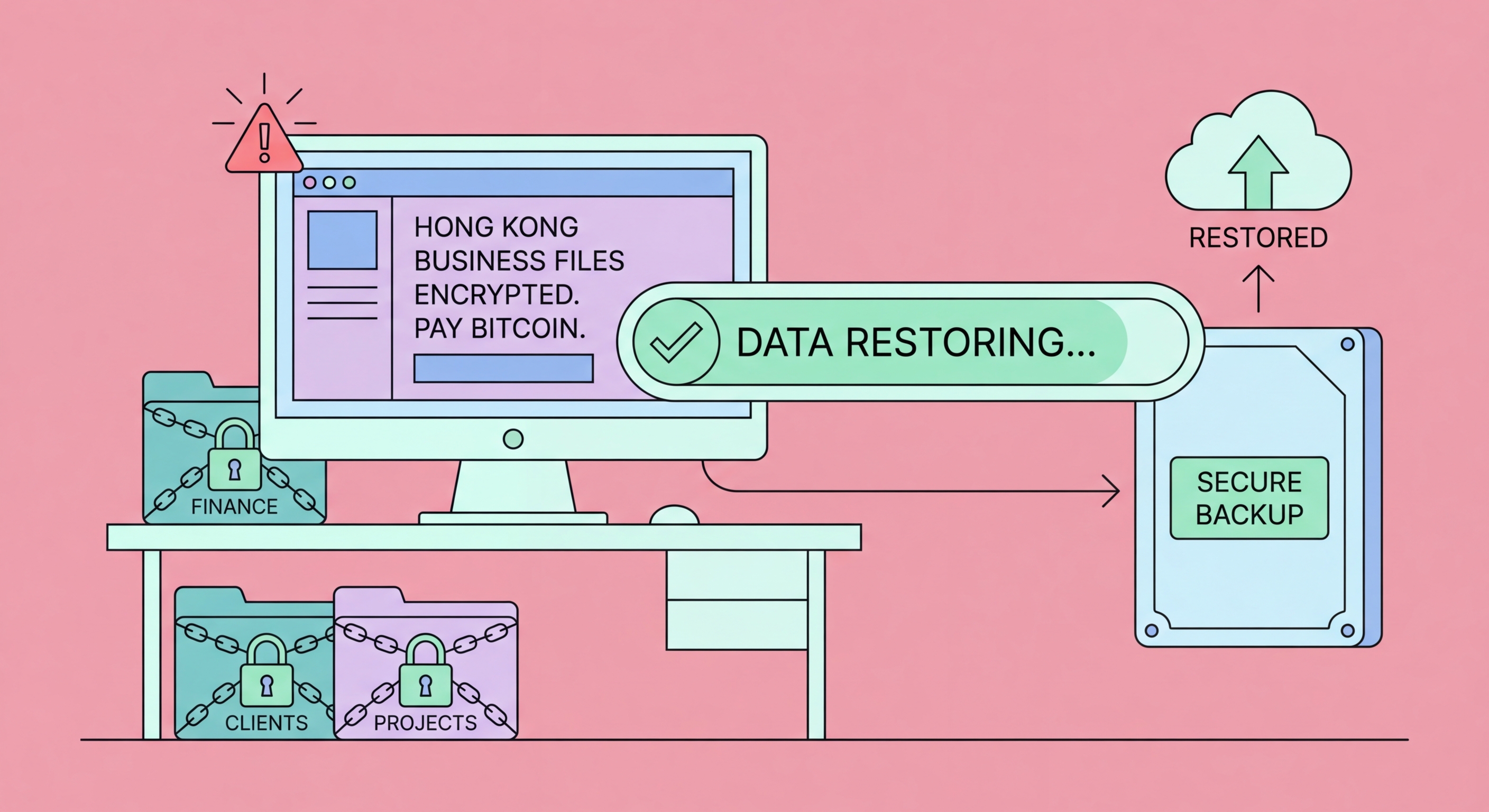
The ransomware attack lifecycle typically unfolds over days to weeks. Initial access occurs through phishing emails, exploitation of unpatched VPN or Remote Desktop Protocol (RDP) vulnerabilities, compromised credentials, or supply chain compromise through a managed service provider. Following initial access, attackers spend time in the network performing reconnaissance — mapping systems, identifying domain controllers and backup infrastructure, escalating privileges, and moving laterally to reach high-value targets. This dwell period, which may last weeks without detection, allows attackers to ensure maximum impact when encryption is finally deployed. Before encrypting, modern ransomware operators exfiltrate sensitive data to leverage in "double extortion" — threatening to publish stolen data publicly if ransom is not paid in addition to refusing to provide decryption keys.
Double extortion has become standard practice for major ransomware groups targeting HK businesses, fundamentally changing the risk calculus. Historically, organisations with tested backups could recover without paying ransom. With double extortion, even organisations that successfully restore from backup face the threat of sensitive customer data, financial records, and business correspondence being published on ransomware group leak sites. For Hong Kong businesses subject to PDPO obligations, this creates a data breach notification requirement independent of whether systems are restored. Industries with strict confidentiality obligations — legal, medical, financial — face particularly severe reputational consequences from data publication, creating pressure to pay even when technical recovery is possible.
- RaaS business model: Modern ransomware is operated by criminal enterprises using affiliate structures — sophisticated, targeted attacks rather than opportunistic malware
- Extended dwell time: Attackers spend days to weeks in networks before encrypting — early detection during this dwell period can prevent encryption entirely
- VPN and RDP targeting: Unpatched VPN appliances and exposed RDP are the most common initial access vectors for ransomware targeting HK businesses
- Double extortion: Data exfiltration before encryption means even organisations with clean backups face data breach consequences — backup alone is no longer a complete defence
- Backup destruction: Ransomware operators specifically seek and destroy backup copies during dwell time — accessible backups are not safe backups
- HK sector targeting: Financial services, professional services, and logistics companies in HK are high-value ransomware targets due to data sensitivity and operational dependence on systems