2Network and Email Security
Network Security and Email Protection Checklist
Network security for Hong Kong businesses requires a business-grade firewall as the minimum perimeter control. The ISP-provided routers from HKT, HKBN, or SmarTone that many SMEs rely on are inadequate for business security — they lack intrusion prevention, web filtering, application control, and the security update cadence that business firewalls provide. Deploying a UTM firewall from Sophos, Fortinet, or WatchGuard creates the perimeter control needed to implement meaningful network security. The firewall must be actively maintained: firmware updates applied within 14 days of release, rules reviewed quarterly, and IPS and web filtering subscriptions renewed to maintain current threat intelligence.
Email security is critical given that phishing is the primary initial access vector for attacks against HK businesses. The three-layer email security stack — DMARC/DKIM/SPF authentication to prevent domain spoofing, email security gateway scanning for malicious attachments and links, and employee phishing simulation training — addresses the technical, procedural, and human dimensions of email threat. DMARC at p=reject enforcement prevents your domain from being used to send phishing emails impersonating your business. Microsoft Defender for Office 365 (included in M365 Business Premium) or a third-party email gateway provides sandboxing of attachments and time-of-click URL inspection. An external email warning banner on all inbound email helps employees visually distinguish external from internal senders.
Network segmentation limits the blast radius when a device is compromised. The flat network architecture common in many HK SME offices — where all devices can communicate with all other devices freely — means a single compromised workstation can reach every server, every file share, and every backup location on the network. VLAN-based segmentation separating workstations from servers, isolating backup infrastructure, and placing IoT devices on separate segments significantly limits lateral movement. DNS filtering — routing all DNS queries through Cloudflare Gateway or Cisco Umbrella — provides a network-level blocking layer for malware command-and-control communication and phishing site access, protecting all devices on the network without requiring per-device software changes.
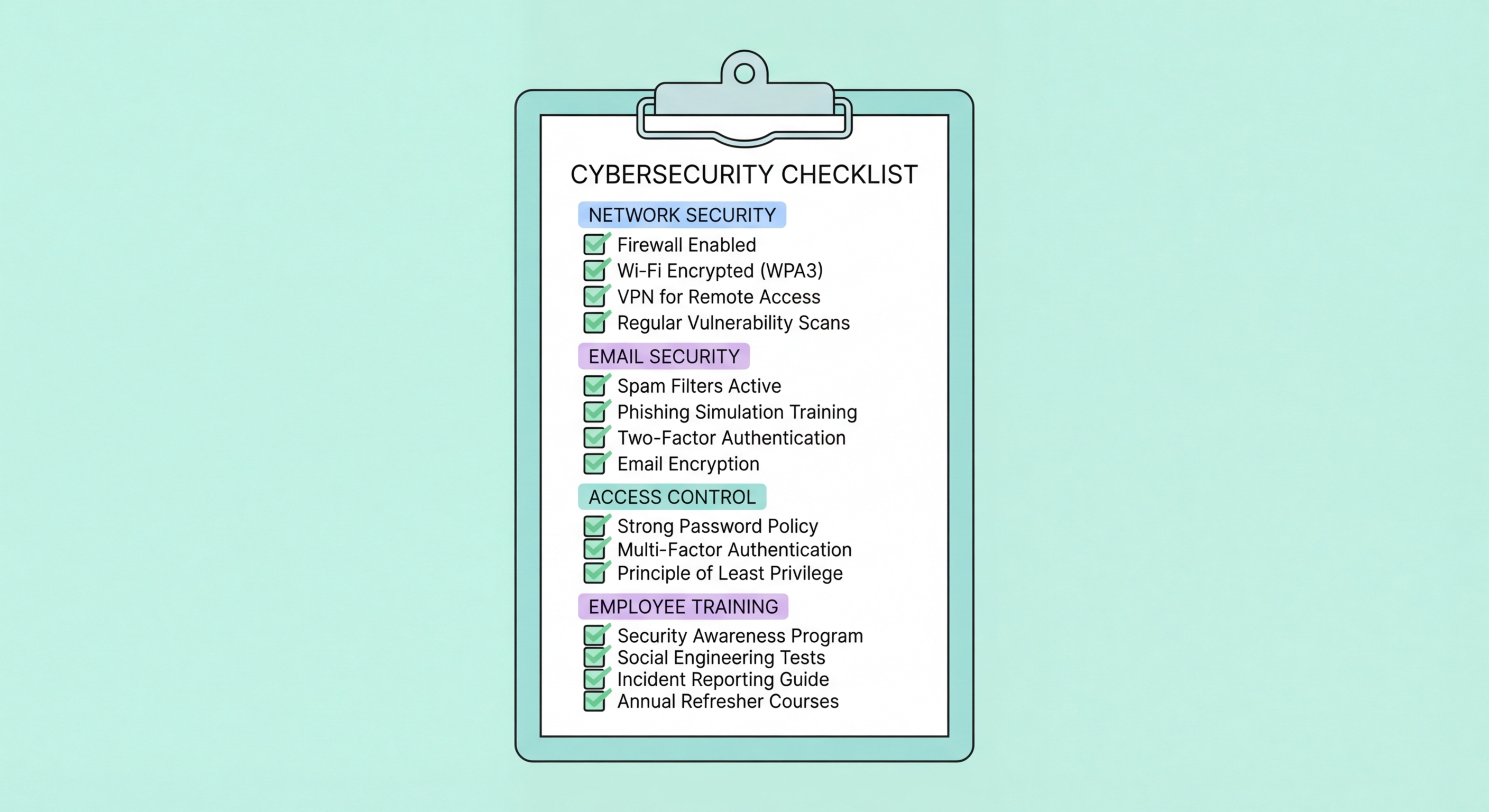
- Business UTM firewall deployed: Business-grade UTM firewall with IPS and web filtering replacing ISP router — firmware current, rules documented and reviewed quarterly
- DMARC at p=reject: DMARC, DKIM, and SPF configured for all owned domains with DMARC progressed to p=reject enforcement — prevents domain spoofing
- Email security gateway: Microsoft Defender for Office 365 or equivalent email gateway with attachment sandboxing and URL inspection — safe attachments and safe links enabled
- External email banners: Visual warning banner on all externally-sourced email — helps employees identify non-internal senders
- Network segmentation: VLANs separating workstations from servers — backup infrastructure isolated from workstation network access
- DNS filtering: All network DNS queries routed through Cloudflare Gateway or equivalent — blocks malicious domains and phishing sites network-wide