2Account Lifecycle Management
User Account Lifecycle Management: Joiner, Mover, Leaver
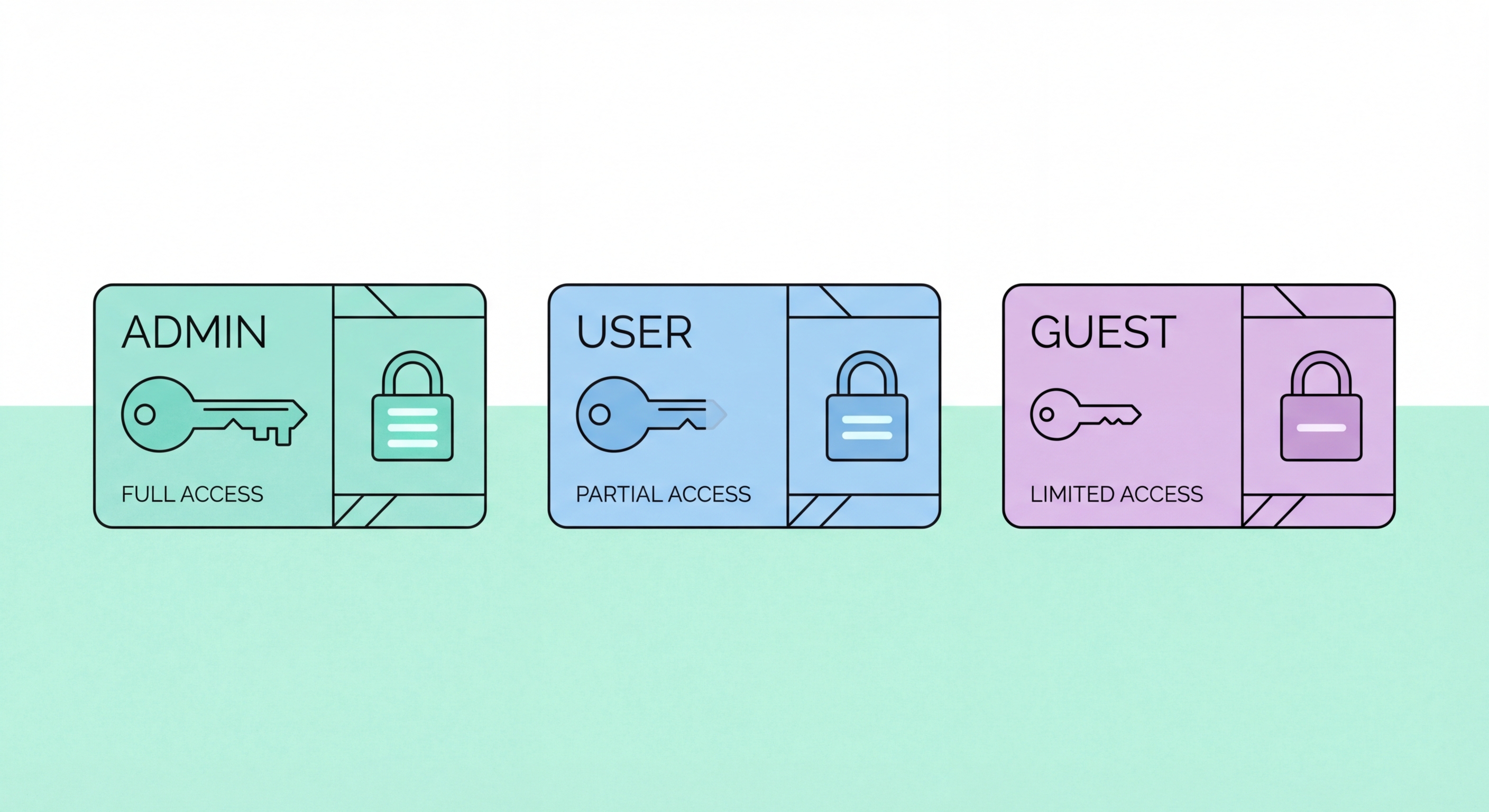
Account lifecycle management — the processes governing how user accounts are created, modified, and deactivated — is where access control policy translates into operational practice. Three lifecycle events require specific procedures: joiners (new employees requiring account provisioning), movers (employees changing roles or departments whose access needs to change), and leavers (employees departing the organisation whose access must be promptly revoked). Each of these events is a point of access control risk. Failure to provision accounts correctly creates early over-permission. Failure to update access for role changes creates stale permissions. Failure to promptly deactivate leaver accounts creates ongoing access risk from former employees or their compromised credentials.
Leaver account deactivation is the most time-sensitive account lifecycle event. When an employee departs — whether voluntarily or involuntarily — their access to all systems must be revoked on or before their last day of employment. For involuntary departures (dismissal), access should be revoked simultaneously with notification to prevent data theft or sabotage. A leaver checklist should cover all access types: Active Directory or Microsoft Entra account deactivation, Microsoft 365 or Google Workspace account deactivation, VPN credentials revocation, cloud application access removal (Xero, Salesforce, HubSpot), physical access revocation (building access cards), and handover of any shared credentials held by the leaver (this also triggers those shared credentials requiring immediate rotation).
Orphaned accounts — accounts that remain active after the user they were created for has left or changed roles — are among the most commonly exploited access control weaknesses. Attackers who obtain a list of valid account names (easily obtained from many systems) can target dormant accounts that may not have password reset requirements, multi-factor authentication, or active monitoring, since these accounts never generate unusual activity baseline violations. Regular account audits comparing active accounts against current HR records identify orphaned accounts for deactivation. Microsoft Entra ID's access review feature, and equivalent functionality in Google Workspace Admin, can automate periodic access review workflows for HK businesses with cloud-based identity management.
- Joiner provisioning checklist: Document the specific access grants for each role — new accounts are provisioned to the role profile, not ad hoc
- Same-day leaver deactivation: Deactivate all access on the employee's last day — for involuntary departures, deactivation occurs simultaneously with notification
- Leaver access checklist: Create a comprehensive checklist covering AD, Microsoft 365, VPN, cloud apps, and physical access — partial deactivation leaves residual access risk
- Role change access adjustment: When employees change roles, remove access specific to their old role and add access for the new role — do not simply add new access while retaining old
- Quarterly orphaned account audit: Compare active accounts against current HR records quarterly — deactivate accounts for departed employees immediately upon discovery
- Contractor and vendor accounts: Contractor accounts must have defined expiry dates — temporary access that becomes permanent is a common orphaned account source